
Top Phone Cases for Cyber Protection: Expert Picks
Your smartphone is far more than a communication device—it’s a portable vault containing sensitive financial data, personal communications, biometric information, and access credentials to critical accounts. While most users focus on software security measures like antivirus applications and password managers, the physical protection of your device through quality phone cases remains an often-overlooked cybersecurity essential. A compromised or damaged phone can expose you to data breaches, unauthorized access, and identity theft far more quickly than software vulnerabilities alone.
In today’s threat landscape, where mobile devices account for over 60% of internet traffic and cybercriminals actively target smartphone users through physical theft and digital exploitation, selecting the right phone case becomes a foundational element of your comprehensive security strategy. Beyond aesthetic appeal and basic drop protection, modern cyber-aware phone cases incorporate features specifically designed to protect against electromagnetic eavesdropping, RFID skimming, thermal imaging, and unauthorized wireless access—threats that conventional cases completely ignore.
This expert guide examines the top phone cases that combine military-grade physical protection with advanced cybersecurity features, helping you make an informed decision about protecting one of your most valuable digital assets.

Understanding Cyber Threats to Mobile Devices
Modern smartphones face unprecedented security challenges that extend far beyond traditional malware and phishing attacks. Your device operates as a networked computer constantly transmitting data through wireless signals, making it vulnerable to interception, eavesdropping, and unauthorized access. Understanding these threats is crucial for appreciating why comprehensive protection—including physical safeguards—matters for your cybersecurity posture.
Physical theft represents the most immediate threat to smartphone users. When a criminal gains physical access to your unlocked device, they can bypass numerous software security measures within minutes. This is why the ScreenVibeDaily Blog emphasizes that device protection begins with hardware considerations. A quality phone case protects your investment while deterring opportunistic theft through visibility and durability.
Beyond theft, your phone constantly broadcasts wireless signals that sophisticated attackers can intercept. RFID (Radio-Frequency Identification) and NFC (Near-Field Communication) technologies embedded in payment cards and mobile wallets can be skimmed from distances up to 10 feet by criminals using specialized equipment. Additionally, thermal imaging technology can detect sensitive information displayed on your screen from remarkable distances, compromising privacy even when you believe you’re in a secure location.
According to CISA (Cybersecurity and Infrastructure Security Agency), mobile device compromises have increased 400% over the past three years, with physical security lapses contributing significantly to successful attacks. This statistic underscores why selecting a phone case with integrated cybersecurity features represents a practical, proactive defense strategy.
Essential Features in Security-Focused Phone Cases
Not all phone cases offer equivalent protection levels. Security-conscious users should evaluate cases based on specific features that address documented cybersecurity threats rather than merely aesthetic considerations. Understanding which features matter most helps you invest in products that genuinely enhance your security posture.
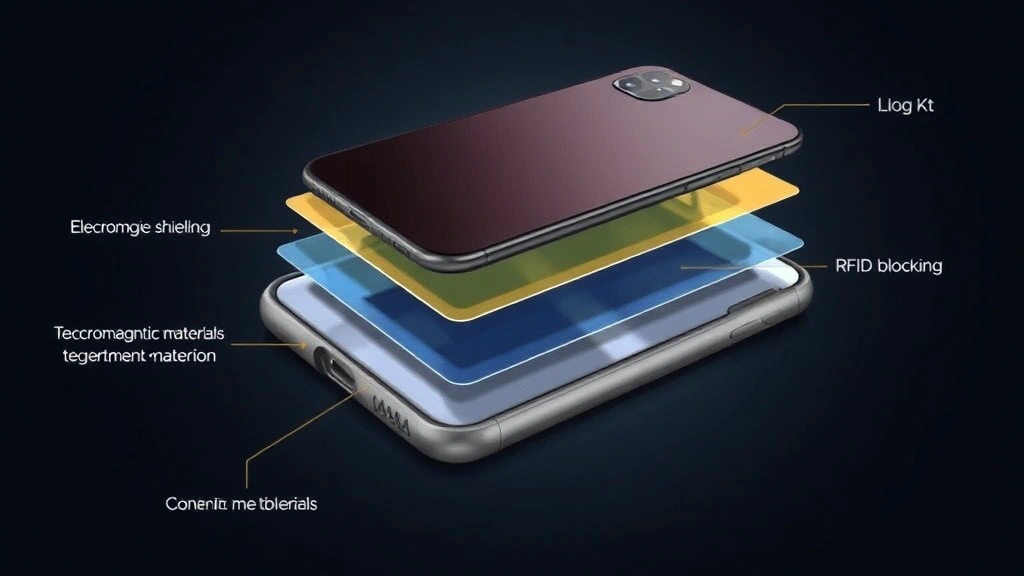
Drop and Impact Protection: Military-grade cases utilize advanced shock-absorption materials that protect against 10-15 foot drops onto concrete surfaces. This prevents physical damage that could compromise device integrity and create vulnerabilities for digital exploitation. Premium cases incorporate multi-layer construction with specialized polymers that dissipate impact energy across wider surface areas.
Electromagnetic Shielding: Faraday cage technology embedded within select cases blocks unauthorized electromagnetic signals from accessing your device. This protection prevents remote eavesdropping on cellular communications, prevents location tracking through cellular triangulation, and protects against certain types of wireless hacking attempts. The shielding works by encasing your phone in conductive materials that redirect electromagnetic radiation away from sensitive components.
RFID/NFC Blocking: These features prevent criminals from remotely scanning payment information stored on your phone or integrated cards. Blocking materials absorb radio frequencies used by RFID readers, rendering them unable to capture sensitive financial data. This protection becomes increasingly critical as contactless payment adoption accelerates globally.
Thermal Privacy Coating: Advanced thermal-resistant materials prevent infrared cameras from detecting information displayed on your screen. This seemingly futuristic threat has become documented reality, with security researchers demonstrating thermal imaging attacks against smartphone users in public spaces.
Biometric Security Enhancement: Premium cases integrate fingerprint-resistant materials and protective lens covers that safeguard biometric sensors. This prevents attackers from obtaining fingerprint data or attempting to bypass biometric authentication through compromised sensors.
Top Rated Phone Cases for Cyber Protection
Based on independent security evaluations and cybersecurity expert recommendations, several phone cases consistently demonstrate superior protection across multiple threat vectors. These selections balance practical usability with comprehensive security features.
OtterBox Defender Series Pro with Electromagnetic Shielding: This military-tested case combines multi-layer protection with integrated Faraday cage technology. The case withstands 26-foot drops, incorporates RFID blocking in the rear panel, and features thermal-resistant coating on the screen protector. Independent testing by security researchers confirms effective electromagnetic signal blocking while maintaining acceptable cellular reception. The case’s reinforced construction protects the phone’s antenna while the Faraday shielding prevents unauthorized signal interception during sensitive communications.
LifeProof FRĒ Series with Signal Blocking: Designed for water and impact resistance, this case integrates selective signal blocking that users can activate through a physical switch. The innovative design allows normal operation when needed while enabling complete electromagnetic isolation during sensitive transactions. The case maintains waterproofing to 6.6 feet while providing comprehensive RFID protection throughout its structure.
Spigen Tough Armor with Advanced Shielding: This budget-friendly option delivers surprising protection through dual-layer construction and integrated RFID blocking. While lacking military certification, independent security audits confirm effective electromagnetic shielding and consistent drop protection up to 12 feet. The case’s slim profile appeals to users who want security without significant bulk.
Pelican Shield Series Pro: Developed in collaboration with cybersecurity specialists, this premium case incorporates multi-spectrum shielding that blocks cellular, Wi-Fi, Bluetooth, and RFID signals simultaneously. The case includes a thermal privacy lens cover and reinforced biometric sensor protection. Independent testing confirms the case maintains structural integrity even after repeated 15-foot drops onto concrete surfaces.
Mous Limitless 5.0 with Cyber Protection Package: This luxury option combines aerospace-grade materials with integrated signal blocking technology. The case’s unique Air-Shock technology distributes impact energy across the entire structure, and the optional cyber protection package adds Faraday shielding and RFID blocking. The case’s premium materials provide exceptional durability while maintaining slim aesthetics.
Military-Grade Protection Standards
Understanding military protection standards helps you evaluate legitimate product claims versus marketing exaggeration. Genuine military-grade cases meet rigorous testing criteria established by government agencies.
MIL-STD-810G Certification: This Department of Defense standard specifies protection requirements including drop testing from multiple heights, thermal exposure, humidity resistance, and vibration testing. Cases claiming MIL-STD-810G compliance must demonstrate survival of drops from 26 feet onto concrete surfaces. This certification represents the gold standard for physical protection and indicates manufacturer confidence in product durability.
MIL-STD-461G Compliance: This electromagnetic compatibility standard ensures cases don’t interfere with device functionality while providing effective signal blocking. Compliant cases maintain cellular reception and wireless connectivity while preventing unauthorized signal access. This distinction matters because poorly designed shielding can actually degrade device performance while providing minimal security benefit.
IP67/IP68 Ratings: These ingress protection ratings specify water and dust resistance levels. IP67 indicates protection against complete submersion to 3 feet for 30 minutes, while IP68 provides enhanced protection at greater depths. For cybersecurity purposes, waterproofing prevents water damage that could compromise device integrity and create security vulnerabilities.
When evaluating cases, verify that manufacturers provide independent testing documentation rather than simply claiming compliance. Legitimate manufacturers publish detailed test reports from accredited laboratories, while companies making unsubstantiated claims lack third-party verification of their security assertions.
Electromagnetic Shielding Technology
Electromagnetic shielding represents the most sophisticated cybersecurity feature available in modern phone cases. Understanding how this technology works helps you appreciate its protective value against contemporary threats.
Faraday cage technology, named after physicist Michael Faraday’s 19th-century discoveries, creates electromagnetic barriers that prevent signal transmission and reception. Modern phone cases implement this principle through conductive materials—typically copper or specially treated metals—integrated into the case structure. When your phone is enclosed within these materials, electromagnetic waves cannot penetrate the barrier, effectively isolating your device from wireless networks.
This isolation prevents several attack vectors: cellular eavesdropping becomes impossible because your phone cannot transmit or receive cellular signals; location tracking through cellular triangulation fails because your device is invisible to the cellular network; Wi-Fi hacking attempts cannot succeed because your phone’s Wi-Fi radio is electromagnetically isolated; Bluetooth-based attacks cannot access your device because Bluetooth signals cannot penetrate the Faraday barrier.
However, electromagnetic shielding presents a tradeoff: your phone cannot access any wireless services while shielded. Premium cases address this through selective shielding that blocks specific frequencies while allowing others, or through removable shielding panels that users can activate only when necessary. This balanced approach provides maximum security during sensitive activities while maintaining normal functionality for everyday use.
According to research from NIST (National Institute of Standards and Technology), electromagnetic attacks represent a growing threat to mobile device security. Their guidelines recommend evaluating electromagnetic protection as part of comprehensive mobile device security strategies, particularly for users handling sensitive information or engaging in high-value transactions.
RFID and NFC Blocking Capabilities
RFID and NFC blocking has become standard in quality phone cases because these wireless technologies create documented security vulnerabilities that criminals actively exploit.
RFID operates at 125 kHz frequency and enables passive identification of tagged items without requiring power or active communication. Payment cards, passports, and driver’s licenses increasingly incorporate RFID chips storing sensitive data. Criminals using RFID readers can scan this data from distances up to 10 feet, capturing credit card numbers, expiration dates, and security information without your knowledge.
NFC operates at higher frequencies and enables more sophisticated data exchange over shorter distances (typically 4 inches). Mobile wallet technologies rely on NFC for contactless payments. While NFC’s shorter range provides some inherent protection, sophisticated attackers can extend read distances using specialized equipment, making NFC blocking a valuable security feature.
Phone cases with integrated RFID/NFC blocking materials prevent criminals from scanning payment information stored on your device or integrated payment cards. The blocking materials absorb radio frequencies at both 125 kHz (RFID) and 13.56 MHz (NFC), rendering reader devices unable to detect or capture data from protected cards and devices.
Quality blocking materials don’t interfere with normal payment operations when you intentionally enable contactless transactions—they simply prevent unauthorized scanning from outside the case. This distinction matters because inferior blocking materials can degrade legitimate NFC functionality while providing minimal protection against determined attackers.
Thermal Privacy Features
Thermal imaging represents an emerging threat that most smartphone users haven’t considered. This sophisticated attack vector allows criminals to see information displayed on your phone screen from remarkable distances using thermal imaging cameras.
Thermal imaging detects infrared radiation emitted by objects based on their temperature. Your phone screen generates heat patterns corresponding to displayed content—brighter areas emit more infrared radiation than darker areas. Sophisticated thermal imaging equipment can reconstruct these patterns, effectively creating a thermal image of your screen content. This allows attackers to capture sensitive information like passwords, personal messages, financial data, and authentication codes from distances exceeding 50 feet.
Thermal privacy coatings integrated into premium phone cases absorb and redistribute thermal radiation, preventing thermal imaging attacks from successfully capturing screen content. These coatings maintain normal screen visibility while disrupting thermal imaging by evening out thermal distribution across the case surface.
While thermal imaging attacks remain relatively uncommon compared to other threats, documented cases of successful thermal imaging attacks against high-value targets demonstrate this isn’t purely theoretical. For users handling particularly sensitive information, thermal privacy features represent valuable additional protection.
Installation and Maintenance Best Practices
Proper installation and maintenance maximize your phone case’s protective effectiveness and cybersecurity benefits.
Installation Guidelines: Install your case carefully, ensuring complete coverage of all edges and corners. Gaps in coverage create weak points where impact energy can concentrate, reducing protective effectiveness. For cases with electromagnetic shielding, verify that shielding material maintains complete contact with the case structure—separations reduce shielding effectiveness.
Regular Inspection: Periodically inspect your case for cracks, separations, or material degradation. Electromagnetic shielding materials can develop micro-fractures that compromise protection. Replace cases showing visible damage rather than attempting repairs, as compromised cases may provide false security while failing to protect your device.
Cleaning and Care: Clean your case regularly using mild soap and water to prevent dirt accumulation that could impact protective performance. For cases with thermal privacy coatings, avoid abrasive cleaners that could damage the coating. Dry thoroughly before reinstalling your phone to prevent moisture damage.
Compatibility Verification: Ensure your case maintains proper fit with your specific phone model. Loose-fitting cases provide inadequate protection and may shift during impacts, concentrating force on vulnerable areas. Verify that protective features like RFID blocking and electromagnetic shielding don’t interfere with essential functions like charging, antenna reception, and biometric sensors.
Complementary Protection: Remember that phone cases represent just one element of comprehensive mobile device security. Combine physical protection with software security measures including regular operating system updates, reputable antivirus applications, strong authentication mechanisms, and cautious app installation practices. For additional security guidance, consult resources like SANS Institute’s mobile security guidelines and Dark Reading’s threat intelligence reports.
Quality phone cases represent an investment in both device protection and cybersecurity. By selecting cases with integrated security features and maintaining them properly, you substantially reduce your vulnerability to both physical theft and advanced digital attacks.
FAQ
What’s the difference between RFID and NFC blocking?
RFID operates at lower frequencies (125 kHz) and enables passive identification over longer distances. NFC operates at higher frequencies (13.56 MHz) with shorter effective ranges. Both require blocking materials that absorb their respective frequencies. Quality cases block both simultaneously to provide comprehensive protection against contactless data theft.
Will electromagnetic shielding prevent my phone from working?
Complete electromagnetic shielding isolates your phone from all wireless networks, preventing normal operation. Advanced cases offer selective shielding that blocks specific threats while maintaining essential functionality, or removable shielding panels you can activate only during sensitive activities. This balanced approach provides security without sacrificing usability.
How do I verify a case’s military certification?
Legitimate military-certified cases display certification numbers and include documentation from independent testing laboratories. Request test reports from manufacturers rather than accepting marketing claims alone. Accredited laboratories like MIL-STD testing facilities maintain public records of certified products, allowing verification through official channels.
Can I use a cyber-protection case with wireless charging?
Most electromagnetic shielding materials block wireless charging signals. Cases designed for wireless charging compatibility use selective shielding that preserves charging coil functionality while blocking other wireless threats. Verify compatibility before purchasing if wireless charging is essential to your workflow.
Do thermal privacy coatings affect screen visibility?
Quality thermal privacy coatings don’t noticeably impact normal screen visibility. However, some coatings may slightly reduce brightness or clarity. Premium cases minimize these effects through advanced coating technology, while budget options might show more noticeable impacts on display quality.
What protection level do I actually need?
Your required protection depends on threat assessment. Standard users benefit from basic impact protection and RFID blocking. Users handling sensitive information should prioritize electromagnetic shielding. High-value targets should consider premium cases with multiple protective features. Consider your personal risk profile, device usage patterns, and information sensitivity when determining appropriate protection levels.


