
Are Arm Protection Sleeves Secure? Expert Insights on Physical Device Security
In an increasingly interconnected world where cyber threats extend beyond digital boundaries, physical security has become a critical component of comprehensive protection strategies. Arm protection sleeves—specialized garments designed to shield devices and sensitive equipment from unauthorized access, electromagnetic interference, and environmental hazards—represent an emerging frontier in cybersecurity. But the question remains: are these protective solutions truly secure, or do they present a false sense of confidence?
This comprehensive guide examines the security efficacy of arm protection sleeves, their role in a layered defense strategy, and what cybersecurity experts recommend for organizations seeking to protect their most valuable assets. Whether you’re managing sensitive computing devices, protecting biometric data collection systems, or safeguarding personnel working with classified information, understanding the capabilities and limitations of arm protection sleeves is essential for making informed security decisions.

Understanding Arm Protection Sleeves in Cybersecurity Context
Arm protection sleeves represent a specialized category of physical security equipment designed to create a protective barrier between sensitive devices, biometric sensors, and potential threat vectors. Unlike traditional protective gear, security-focused arm protection sleeves incorporate advanced materials engineered to resist multiple attack vectors simultaneously—from electromagnetic pulse (EMP) interference to unauthorized RFID scanning and thermal imaging attempts.
The fundamental principle underlying arm protection sleeves is layered security—the same concept that governs comprehensive cybersecurity frameworks. Just as organizations implement firewalls, intrusion detection systems, and endpoint protection in digital environments, physical security requires multiple overlapping defenses. Arm protection sleeves serve as the outermost physical layer, protecting devices and biometric systems that may otherwise be vulnerable to direct manipulation or wireless interception.
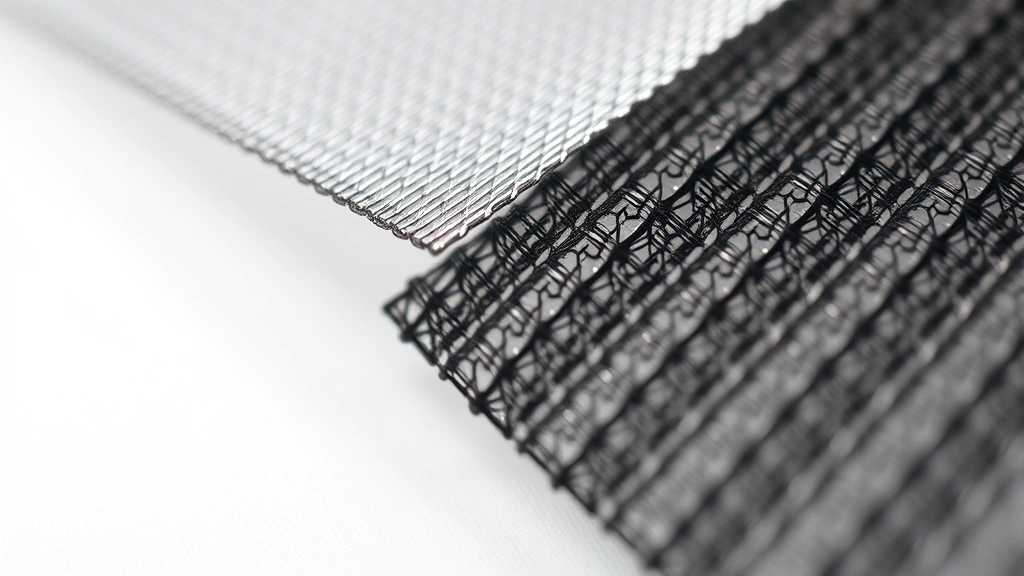
These sleeves typically incorporate several key technologies: conductive mesh materials for electromagnetic shielding, RFID-blocking fabrics that prevent unauthorized wireless scanning, reflective thermal materials to defeat infrared imaging, and durable construction that prevents unauthorized access or tampering. The effectiveness of each component depends heavily on proper material selection, manufacturing quality, and appropriate implementation within a broader security framework.
Physical Security and Cyber Threat Integration
Modern cybersecurity threats increasingly blur the line between digital and physical attacks. CISA (Cybersecurity and Infrastructure Security Agency) has documented numerous incidents where physical access to devices enabled sophisticated cyber compromises. Attackers employing supply chain manipulation, device interception, and hardware implantation techniques require physical proximity to vulnerable equipment.
Arm protection sleeves address this integration point by creating a protective perimeter around devices during transport, storage, and high-risk operational scenarios. Personnel handling sensitive computing devices, biometric collection systems, or classified communication equipment benefit from the additional layer of protection that these sleeves provide. The security value extends beyond the device itself—arm protection sleeves also protect the user wearing the device from biometric theft, thermal signature capture, and electromagnetic eavesdropping.
Consider a scenario involving field operatives collecting biometric data for intelligence purposes. Unprotected wearable devices could be vulnerable to: unauthorized RFID scanning capturing credential data, thermal imaging revealing device locations and operational patterns, electromagnetic emissions analysis extracting sensitive information, and physical tampering during transport or in contested environments. Properly implemented arm protection sleeves mitigate each of these threat vectors simultaneously.
Electromagnetic Shielding Effectiveness
One of the primary functions of advanced arm protection sleeves is electromagnetic interference (EMI) shielding. Electromagnetic shielding effectiveness is measured in decibels (dB), with higher values indicating greater protection against unwanted electromagnetic signals. Quality arm protection sleeves incorporate materials rated for 40-60 dB shielding effectiveness across critical frequency bands, comparable to professional-grade Faraday cage constructions.
The conductive mesh layers within these sleeves work by creating a conductive barrier that redirects electromagnetic energy away from protected devices. This prevents both outbound emissions (protecting against signal eavesdropping) and inbound interference (protecting against jamming or induced attacks). Organizations working with sensitive communications equipment, cryptographic systems, or classified data processing benefit significantly from this dual-directional protection.
However, electromagnetic shielding effectiveness depends critically on proper implementation. Gaps in coverage, poor grounding connections, or inadequate mesh density can substantially reduce protective capabilities. Additionally, shielding effectiveness varies across frequency ranges—a sleeve rated for 40 dB protection at 1 GHz may provide significantly less protection at 10 GHz or higher frequencies. Professional assessment by electromagnetic compatibility (EMC) specialists is recommended for high-security applications.
Real-world testing by cybersecurity researchers has demonstrated that properly constructed arm protection sleeves can reduce electromagnetic emissions by 90-95% when devices are fully enclosed and properly grounded. However, partial coverage or improper material selection can reduce effectiveness to 50% or lower, providing a false sense of security rather than genuine protection.
Biometric and Data Interception Prevention
Biometric systems represent increasingly attractive targets for sophisticated attackers. Fingerprint readers, iris scanners, and facial recognition systems integrated into wearable devices or worn as external sensors can be compromised through unauthorized access, spoofing attacks, or wireless signal interception. Arm protection sleeves address these vulnerabilities by preventing direct physical access and blocking wireless scanning attempts.
RFID-blocking technology integrated into arm protection sleeves prevents unauthorized credential reading from access badges and security tokens. NIST guidelines on physical access control recommend layered verification approaches, with arm protection sleeves serving as the initial barrier preventing passive scanning of credentials. This proves particularly valuable in high-security facilities where unauthorized credential duplication could enable facility breaches or resource theft.
For biometric collection and verification systems, arm protection sleeves prevent several attack vectors: biometric template theft through unauthorized device scanning, presentation attacks where attackers attempt to spoof biometric readers using photographs or synthetic samples, and thermal signature capture that could reveal device locations or operational patterns. By maintaining physical separation between the biometric sensor and potential attackers, arm protection sleeves significantly increase the effort and resources required for successful compromise.
Organizations implementing arm protection sleeves for biometric security report substantial improvements in system integrity. However, effectiveness depends on comprehensive implementation—partial protection or gaps in coverage can allow attackers to target specific components, rendering the protection ineffective.
Industry Standards and Compliance Requirements
Several formal standards govern electromagnetic shielding and physical security for sensitive equipment. MIL-STD-461 (military electromagnetic interference and compatibility standards) and IEEE 299 (standard method for measuring effectiveness of electromagnetic shielding enclosures) provide technical frameworks for evaluating shielding effectiveness. Organizations subject to these standards must ensure arm protection sleeves meet or exceed specified performance requirements.
For classified information systems, NSA/CSS specifications provide detailed requirements for physical protection of cryptographic equipment and sensitive communications devices. While arm protection sleeves alone cannot satisfy comprehensive classified system protection requirements, they serve as valuable components within broader compliance frameworks. Organizations handling classified information should consult with security officers and compliance specialists before implementing arm protection sleeves.
NIST Cybersecurity Framework emphasizes the importance of physical security as a foundational component of comprehensive security programs. Arm protection sleeves align with this framework by addressing the “Protect” function, specifically the physical access control and device protection categories. However, compliance requires proper documentation, testing, and integration within broader security policies and procedures.
Healthcare organizations subject to HIPAA requirements benefit from arm protection sleeves when protecting biometric collection systems and portable medical devices. Financial institutions regulated by PCI DSS can utilize these sleeves for protecting payment processing equipment and credential verification systems. Each regulatory framework requires different implementation approaches and documentation standards.
Real-World Implementation Challenges
Despite their potential security benefits, arm protection sleeves present several practical challenges in real-world operational environments. User acceptance represents a significant barrier—personnel may resist wearing additional protective equipment if it impedes mobility, increases fatigue, or appears visually conspicuous. Security effectiveness is substantially reduced when users disable protection due to discomfort or inconvenience.
Material degradation over time affects shielding effectiveness. Repeated flexing, washing, or environmental exposure can damage conductive mesh layers, reducing electromagnetic shielding from 60 dB to 20-30 dB or lower. Organizations must implement maintenance schedules and periodic testing to verify ongoing protection. This requirement adds operational complexity and cost to security programs.
Thermal management presents another challenge. Arm protection sleeves incorporating reflective thermal materials can trap body heat, potentially causing discomfort during extended wear in warm environments. This may force security officers to choose between thermal protection and user comfort, potentially compromising overall security posture.
Integration with existing security infrastructure requires careful planning. Arm protection sleeves must not interfere with legitimate wireless communications, biometric systems, or device functionality. Improper shielding can block necessary signals, creating operational blind spots or preventing critical system access. Cybersecurity professionals and device manufacturers should collaborate during implementation planning to ensure compatibility.
Cost considerations also affect implementation feasibility. High-quality arm protection sleeves incorporating advanced materials and manufacturing techniques can cost $200-500 per unit, making organization-wide deployment expensive. Cost-benefit analysis should guide purchasing decisions, focusing resources on highest-risk applications and personnel.
Expert Recommendations and Best Practices
Leading cybersecurity researchers and SANS Institute security professionals recommend arm protection sleeves as components of comprehensive physical security programs, not standalone solutions. Effective implementation requires integration with other security measures including: access control systems, surveillance monitoring, personnel security procedures, and incident response protocols.
First recommendation: Conduct threat assessments specific to your operational environment. Identify which devices and personnel face the highest risk from physical compromise, electromagnetic eavesdropping, or biometric theft. Prioritize arm protection sleeve deployment to highest-risk scenarios rather than attempting organization-wide implementation.
Second recommendation: Select sleeves from manufacturers with demonstrated quality standards and third-party testing certifications. Verify electromagnetic shielding effectiveness through independent testing by EMC specialists. Request documentation of material composition, manufacturing processes, and quality assurance procedures. Avoid products making exaggerated security claims without supporting technical evidence.
Third recommendation: Establish maintenance and replacement schedules. Test shielding effectiveness quarterly or semi-annually, depending on usage intensity. Replace sleeves showing degradation or damage immediately—compromised protection provides false security. Document all testing and maintenance activities for compliance purposes.
Fourth recommendation: Integrate arm protection sleeves into broader security awareness training. Personnel must understand why protection is necessary, how to properly use and maintain sleeves, and what threat vectors remain despite sleeve deployment. Incomplete understanding undermines effectiveness—users may disable protection or implement it incorrectly.
Fifth recommendation: Combine arm protection sleeves with digital security measures. Physical protection alone cannot prevent software-based attacks, malware, or network compromise. Ensure devices protected by sleeves also receive comprehensive endpoint protection, regular patching, encryption, and network monitoring. The DARPA cybersecurity research community emphasizes that physical and digital security must work together as integrated systems.
Organizations implementing arm protection sleeves should also consider complementary physical security measures: secure storage facilities with access controls, secure transportation procedures, personnel background checks and security clearances, and regular security audits. Arm protection sleeves represent one component within comprehensive defense-in-depth strategies, not a complete security solution.
FAQ
What threats do arm protection sleeves actually prevent?
Arm protection sleeves effectively prevent: unauthorized RFID scanning of credentials, electromagnetic eavesdropping on device emissions, thermal imaging detection of devices, and direct physical access to device components. They do not prevent software attacks, malware, network compromise, or attacks targeting unprotected portions of systems. Effectiveness depends on proper implementation and maintenance.
How long do arm protection sleeves remain effective?
Quality varies significantly based on materials and manufacturing. Professional-grade sleeves typically maintain 80%+ shielding effectiveness for 12-24 months with normal use. Degradation accelerates with repeated flexing, washing, or exposure to harsh environments. Regular testing every 3-6 months is recommended for high-security applications. Replace sleeves showing visible damage, corrosion, or reduced shielding effectiveness immediately.
Can arm protection sleeves interfere with necessary device functionality?
Yes, improper shielding can block legitimate wireless signals, biometric scanning, or communications. During implementation, test all device functions within protected sleeves to ensure compatibility. Work with device manufacturers and cybersecurity professionals to optimize shielding while maintaining necessary functionality. Some applications may require partial protection or removable sections.
Are arm protection sleeves compliant with regulatory requirements?
Compliance depends on your specific regulatory environment. HIPAA, PCI DSS, and other frameworks recognize physical security as important but don’t specifically mandate arm protection sleeves. However, they can support compliance with physical access control and device protection requirements. Consult compliance specialists and security officers before implementation to ensure proper documentation and integration.
What should organizations look for when selecting arm protection sleeves?
Prioritize: third-party electromagnetic shielding effectiveness testing and documentation, clear material composition and manufacturing standards, user reviews from comparable organizations, warranty and replacement policies, and manufacturer technical support. Avoid products with unsubstantiated claims or no independent testing. Budget $200-500 per quality sleeve and plan for ongoing maintenance costs.


