
Advanced Firewalls: Are They Enough? Expert Insights on Cyber Protection
Advanced firewalls have become the cornerstone of modern cybersecurity infrastructure, yet organizations continue to suffer devastating breaches despite deploying sophisticated firewall solutions. The critical question facing security leaders today isn’t whether advanced firewalls are effective—they demonstrably are—but rather whether they constitute a sufficient standalone defense strategy. As cyber threats evolve at an unprecedented pace, relying exclusively on firewall technology, regardless of sophistication, exposes organizations to significant risk.
The evolution from traditional stateful firewalls to next-generation firewalls (NGFWs) represents a quantum leap in network security capabilities. Modern advanced firewalls integrate application-layer filtering, intrusion prevention systems (IPS), threat intelligence feeds, and behavioral analytics. However, this technological advancement coincides with an equally sophisticated threat landscape where attackers bypass perimeter defenses through insider threats, supply chain compromises, and encrypted traffic exploitation. Understanding the capabilities and limitations of advanced firewalls is essential for building a resilient cybersecurity posture.
What Modern Advanced Firewalls Actually Do
Advanced firewalls represent a significant technological leap from their predecessors. Unlike traditional firewalls that operate at network and transport layers, NGFWs inspect traffic at the application layer, enabling organizations to understand and control what applications are running on their networks. This deep packet inspection (DPI) capability allows security teams to identify encrypted malware, unauthorized applications, and sophisticated attack patterns that legacy firewalls would miss entirely.
Modern advanced firewalls incorporate several critical capabilities: application awareness and control enables granular policy enforcement based on specific applications rather than ports; intrusion prevention systems detect and block known attack signatures and anomalous behavior patterns; threat intelligence integration automatically updates defenses with information about emerging threats; and user identity integration applies security policies based on user roles and risk profiles rather than just IP addresses. Additionally, advanced firewalls often include sandboxing capabilities that detonate suspicious files in isolated environments to detect zero-day exploits.
The sophistication of these systems is undeniable. A modern NGFW can process millions of packets per second while simultaneously analyzing application behavior, correlating events with threat intelligence feeds, and enforcing hundreds of security policies. Organizations implementing advanced firewalls typically see measurable improvements in their ability to detect and prevent common attack vectors, including malware distribution, data exfiltration attempts, and network reconnaissance activities.
The Critical Limitations of Firewall-Only Strategies
Despite their capabilities, advanced firewalls have fundamental limitations that organizations must understand. The most significant limitation stems from their architectural position: firewalls operate at network boundaries and cannot protect against threats originating from within the network. CISA reports that insider threats and compromised internal systems represent an increasingly significant portion of successful cyberattacks, yet firewalls are powerless against these vectors.
Encrypted traffic presents another critical challenge. Modern firewalls can inspect encrypted traffic only if they possess decryption capabilities, a practice that raises significant privacy concerns and performance implications. However, without this capability, firewalls become blind to threats hidden within encrypted communications—a technique increasingly favored by sophisticated threat actors. Studies indicate that over 80% of enterprise traffic is now encrypted, meaning traditional firewall inspection methodologies become progressively less effective.
Advanced firewalls also struggle with sophisticated evasion techniques. Attackers employ tactics such as protocol tunneling, where malicious traffic is encapsulated within legitimate protocols; polymorphic malware that constantly changes its signature to evade detection; and slow-and-low attacks that distribute malicious activity over extended periods to remain below detection thresholds. A firewall analyzing individual packets or connections may miss patterns that become obvious only when analyzing behavior across extended timeframes and multiple data sources.
The zero-day vulnerability problem represents perhaps the most fundamental limitation. By definition, firewalls cannot detect attacks exploiting previously unknown vulnerabilities. While advanced firewalls with behavioral analysis can sometimes identify anomalous activity patterns associated with zero-day exploitation, they lack the specific knowledge required to definitively identify and block such attacks with high confidence.
Additionally, firewalls cannot protect against compromised credentials. When attackers obtain legitimate user credentials—through phishing, password reuse, or credential stuffing attacks—they can authenticate through the firewall using legitimate access. Once inside the network, they operate with the same permissions as the legitimate user, making firewall-based detection extremely difficult.
Multi-Layered Defense: Moving Beyond Perimeter Protection
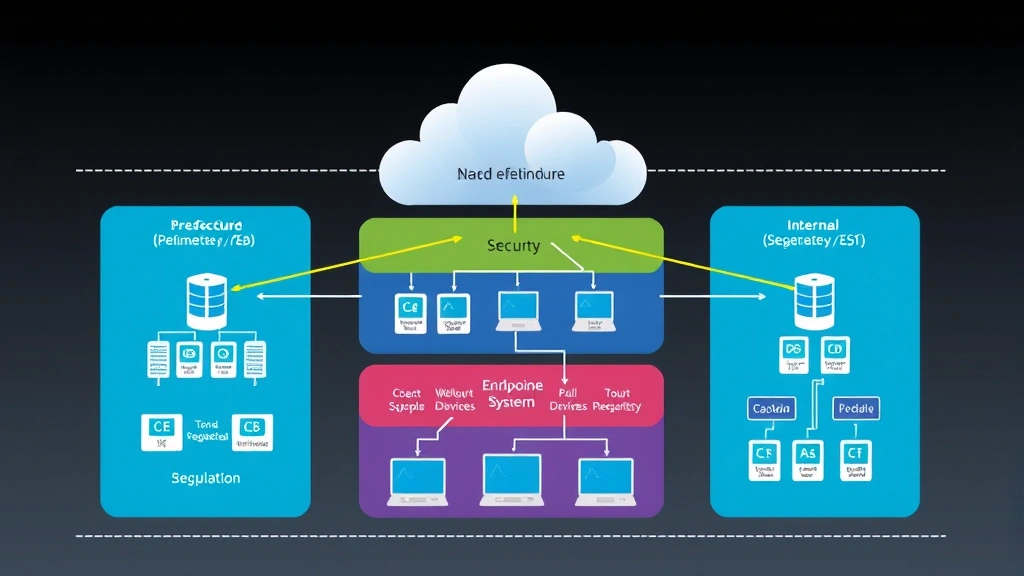
Security experts universally advocate for defense-in-depth strategies that treat advanced firewalls as essential but insufficient components of a comprehensive security architecture. This approach, aligned with NIST Cybersecurity Framework principles, distributes security controls across multiple layers to address the full spectrum of threats.
The first critical addition to firewall protection is endpoint detection and response (EDR) technology. Where firewalls protect network boundaries, EDR solutions monitor individual computers and servers for suspicious behavior, unauthorized privilege escalation, and lateral movement attempts. EDR tools maintain visibility into process execution, file modifications, network connections, and registry changes—activities that firewalls cannot observe. Implementing robust security best practices across your organization provides foundational protection.
Identity and access management (IAM) systems form another essential layer. Advanced firewalls have no mechanism to verify that a user requesting access actually is who they claim to be. Multi-factor authentication, conditional access policies, and zero-trust network access principles ensure that authentication and authorization occur at every stage, not just at the network perimeter. This approach is particularly critical for organizations with remote workers and cloud infrastructure, where traditional perimeter concepts become meaningless.
Network segmentation represents a crucial architectural control that firewalls alone cannot implement effectively. By dividing networks into logical segments with restricted communication between segments, organizations ensure that if attackers compromise one segment, they cannot freely move throughout the entire network. Microsegmentation takes this concept further, creating granular boundaries around individual applications and workloads. Advanced firewalls can enforce segmentation policies, but the segmentation strategy itself must be designed at an architectural level.
Data loss prevention (DLP) systems monitor for attempts to exfiltrate sensitive information, detecting both obvious attacks and subtle data theft. While firewalls can block certain protocols or destinations, they cannot understand the semantic content of data or identify when sensitive information is being transmitted. DLP solutions complement firewall protections by monitoring for suspicious data movement patterns regardless of the underlying protocol or encryption method.
Security information and event management (SIEM) platforms aggregate and analyze logs from firewalls, endpoint devices, servers, and applications to identify coordinated attacks that individual tools might miss. A sophisticated attacker’s activities typically leave traces across multiple systems; SIEM platforms excel at correlating these traces to identify attack patterns that individual tools cannot detect in isolation.
Threat intelligence integration extends beyond the automated feeds that advanced firewalls consume. Security teams should actively monitor threat intelligence from threat intelligence platforms and incident response firms to understand the specific threats targeting their industry and organization. This intelligence should inform not only firewall rules but also incident response procedures, vulnerability management priorities, and security awareness training.
Expert Recommendations for Comprehensive Security
Leading cybersecurity experts consistently recommend a structured approach to integrating advanced firewalls into comprehensive security programs. The recommendations align across industry leaders and align with established frameworks.
Implement Zero-Trust Architecture: Rather than trusting any traffic that originates from inside the network perimeter, zero-trust approaches verify every connection, user, and device regardless of origin. Advanced firewalls serve as enforcement points in zero-trust architectures, but the overall strategy extends far beyond firewall capabilities. Every access request should be authenticated, authorized, and encrypted, with continuous monitoring for anomalous behavior throughout the session.
Establish Continuous Monitoring and Detection: Firewalls excel at preventing known threats but struggle with detection of sophisticated attacks that use evasion techniques. Continuous monitoring through EDR, network traffic analysis (NTA), and user behavior analytics (UBA) enables organizations to identify compromised systems and suspicious activities that firewalls missed. This detection capability is essential because even the most sophisticated firewall cannot prevent all attacks.
Develop Incident Response Capabilities: Despite implementing advanced firewalls and multiple security layers, organizations should assume breach mentality and develop comprehensive incident response capabilities. This includes incident response teams trained to investigate security events, containment procedures to limit damage from successful attacks, and forensic capabilities to understand how attackers bypassed defenses.
Maintain Rigorous Patch Management: Many successful attacks exploit known vulnerabilities that organizations failed to patch. While advanced firewalls can sometimes block exploit attempts, they cannot protect against vulnerabilities in the organization’s own systems. Comprehensive patch management across all systems—operating systems, applications, firmware, and third-party software—represents a critical control that firewalls cannot replace.
Conduct Regular Security Testing: Penetration testing, red team exercises, and vulnerability assessments reveal gaps in security defenses that individual tools cannot identify. These assessments should specifically test whether advanced firewalls can be bypassed, whether lateral movement is possible after initial compromise, and whether data exfiltration can be detected and prevented.
Real-World Case Studies and Breach Analysis
Examining actual security breaches reveals patterns in how organizations with advanced firewalls still suffer compromises. These case studies illustrate the importance of defense-in-depth strategies.
The Target breach of 2013, while predating modern NGFWs, established a pattern that continues today: attackers compromised the organization through a third-party vendor, then moved laterally to access payment systems. A sophisticated firewall cannot prevent lateral movement by a user with legitimate network access. Only network segmentation, monitoring for unusual access patterns, and endpoint-based detection can address this threat vector.
The SolarWinds supply chain attack of 2020 demonstrated that attackers can hide malicious code within legitimate software updates, then use legitimate credentials to access networks. Firewalls examined the initial compromise traffic and found nothing suspicious because the traffic appeared to come from legitimate software. Only behavioral monitoring and threat intelligence indicating unusual activities by the SolarWinds process revealed the compromise.
Recent ransomware campaigns targeting healthcare and critical infrastructure organizations frequently bypass advanced firewalls through compromised credentials obtained via phishing attacks. Once inside the network with legitimate credentials, attackers move laterally and establish persistence—activities that firewalls cannot effectively prevent. Organizations that suffered the most significant damage typically lacked EDR solutions, network monitoring, and incident response capabilities to detect and contain the attack before encryption began.
The MOVEit vulnerability exploitation in 2023 affected thousands of organizations despite many having advanced firewalls deployed. The vulnerability allowed remote code execution on web servers protected by these firewalls. Organizations that suffered data loss typically lacked adequate patch management processes and monitoring for unusual behavior on their web servers. Those that detected compromises quickly had implemented continuous monitoring and threat intelligence that indicated exploitation attempts.

These case studies consistently demonstrate a critical pattern: advanced firewalls prevented initial compromise in some cases but could not detect or prevent lateral movement, privilege escalation, and data exfiltration by attackers who obtained legitimate access or exploited vulnerabilities in protected systems. The organizations that successfully contained attacks had implemented comprehensive security programs extending far beyond firewall capabilities.
Building Your Comprehensive Security Program: Organizations should view advanced firewalls as essential but foundational elements of security programs. The most effective security postures combine advanced firewalls with endpoint protection, identity management, network monitoring, data protection, incident response capabilities, and continuous security testing. This layered approach ensures that even if attackers bypass one control, others detect and prevent further progression.
The question “are advanced firewalls enough?” has a clear answer: no. However, advanced firewalls remain absolutely essential components of modern security architecture. The key is understanding their specific capabilities and limitations, then building comprehensive programs that address threats across the entire attack lifecycle—from initial compromise through lateral movement, privilege escalation, and data exfiltration.
FAQ
What is the difference between a traditional firewall and an advanced firewall?
Traditional firewalls operate at network and transport layers, filtering traffic based on IP addresses, ports, and protocols. Advanced firewalls (NGFWs) add application-layer inspection, enabling understanding of what applications are running, integration of threat intelligence, user identity awareness, and behavioral analysis capabilities that traditional firewalls lack.
Can an advanced firewall detect zero-day attacks?
Advanced firewalls cannot definitively detect zero-day exploits by signature because no signature exists. However, behavioral analysis capabilities may identify unusual activities associated with zero-day exploitation. Comprehensive security programs combine this firewall capability with endpoint monitoring, threat intelligence, and incident response to address zero-day risks.
How do advanced firewalls handle encrypted traffic?
Advanced firewalls can inspect encrypted traffic if they possess decryption capabilities (SSL/TLS inspection), examining the decrypted content for threats. However, this approach raises privacy concerns and performance implications. Without decryption capabilities, firewalls cannot inspect encrypted traffic content, creating a significant blind spot in modern networks where most traffic is encrypted.
What is the relationship between advanced firewalls and zero-trust security?
Advanced firewalls serve as enforcement points in zero-trust architectures, but zero-trust extends far beyond firewall capabilities. Zero-trust requires authenticating every user and device, authorizing every access request, encrypting all communications, and continuously monitoring for anomalous behavior—capabilities that require integration of firewalls with identity systems, endpoint protection, and monitoring tools.
How can organizations detect attacks that bypass their advanced firewall?
Organizations should implement endpoint detection and response (EDR) solutions, network traffic analysis (NTA), user behavior analytics (UBA), and security information and event management (SIEM) platforms. These tools monitor for suspicious activities that bypass firewall detection, including lateral movement, privilege escalation, and data exfiltration attempts.
What is the most common reason organizations with advanced firewalls still suffer breaches?
The most common reason is over-reliance on firewall protection without implementing detection and response capabilities. Organizations focus on prevention but lack visibility into what happens after attackers bypass perimeter defenses. Comprehensive breach response requires combining prevention (firewalls) with detection (EDR, monitoring) and response (incident response teams) capabilities.


