
Secure Virtual Office Login: Expert Best Practices for Admiral Security and Beyond
Remote work has fundamentally transformed how organizations operate, making virtual office access a critical security frontier. Whether you’re accessing an Admiral Security virtual office login system or any enterprise platform, authentication vulnerabilities represent one of the most exploitable attack vectors in modern cybersecurity. A single compromised credential can grant threat actors access to sensitive corporate data, intellectual property, and customer information.
The convergence of distributed workforces, cloud infrastructure, and sophisticated cyber threats demands that security professionals and remote workers understand and implement robust login protocols. This comprehensive guide explores industry-leading best practices for securing virtual office access, protecting your organization’s digital perimeter, and maintaining the integrity of your remote workforce infrastructure.

Understanding Virtual Office Login Threats
Virtual office login systems face an evolving landscape of sophisticated threats. Credential stuffing attacks, where attackers use compromised username and password combinations from previous breaches, represent a persistent danger. Phishing campaigns specifically target remote workers through convincing emails that impersonate legitimate login portals, capturing credentials before users access authentic systems.
Man-in-the-middle (MITM) attacks intercept unencrypted communications between users and login servers, particularly on unsecured Wi-Fi networks. Brute force attacks systematically attempt password combinations to gain unauthorized access. Keyloggers and spyware installed on personal devices capture login credentials as users type them. Additionally, session hijacking allows attackers to steal active session tokens, bypassing initial authentication entirely.
According to the Cybersecurity and Infrastructure Security Agency (CISA), compromised credentials remain the primary attack vector for data breaches across industries. Organizations implementing Admiral Security virtual office login systems must recognize that authentication is not a one-time event but an ongoing security process requiring continuous monitoring and improvement.
The threat landscape extends beyond external attackers. Insider threats—whether malicious or negligent—pose significant risks when employees share credentials, use weak passwords, or fail to secure their access credentials properly. Understanding these diverse threat vectors is the foundation for implementing effective countermeasures.
Multi-Factor Authentication Implementation
Multi-factor authentication (MFA) represents the single most effective defense against unauthorized virtual office access. By requiring multiple verification methods, MFA dramatically increases the difficulty of credential compromise, as attackers must breach multiple security layers simultaneously.
Types of Authentication Factors:
- Something you know: Passwords, PINs, or security questions
- Something you have: Hardware security keys, authenticator apps, or smart cards
- Something you are: Biometric data including fingerprints, facial recognition, or iris scans
- Somewhere you are: Location-based verification or geofencing
For Admiral Security virtual office login and similar enterprise systems, implementing at least two distinct factor types is essential. Hardware security keys like YubiKeys offer exceptional protection because they cannot be remotely compromised or phished. Time-based one-time passwords (TOTP) generated by authenticator applications provide strong protection when properly configured.
Push notification authentication, where users approve login attempts through their mobile devices, combines convenience with security by allowing users to verify they initiated the login attempt. SMS-based one-time passwords, while better than single-factor authentication, are increasingly vulnerable to SIM swapping attacks and should be considered a minimum baseline rather than an optimal solution.
Organizations should mandate MFA for all remote access, with no exceptions for administrative accounts or frequent users. The NIST Digital Identity Guidelines recommend MFA as a fundamental requirement for protecting sensitive systems and data.
Password Management and Credential Security
Despite advances in authentication technology, passwords remain a critical component of virtual office login security. Weak password practices continue to undermine even sophisticated security architectures. Organizations must establish and enforce comprehensive password policies while providing employees with tools to manage credentials effectively.
Password Policy Best Practices:
- Enforce minimum length of 12-16 characters for maximum entropy
- Require complexity including uppercase, lowercase, numbers, and special characters
- Implement regular password changes for high-risk accounts (quarterly minimum)
- Prevent password reuse across the last 12-24 iterations
- Implement account lockout after 5-10 failed login attempts
- Establish password expiration policies with automated reminders
Enterprise password managers like Bitwarden, 1Password, or Dashlane enable employees to maintain unique, complex passwords for each system without relying on memory. These tools generate cryptographically secure passwords and sync across devices, reducing the temptation to reuse weak passwords across multiple platforms. When selecting a password management solution, prioritize vendors with transparent security audits and zero-knowledge architecture.
Credential storage on virtual office login systems must employ industry-standard hashing algorithms like bcrypt, scrypt, or Argon2, never storing passwords in plaintext or reversible encryption. Salting ensures that identical passwords generate different hashes, preventing rainbow table attacks.
Organizations should conduct regular password audits using tools that identify weak credentials, breached passwords found in public databases, and accounts with excessive age. The Have I Been Pwned database allows organizations to check if employee credentials appear in known breach databases, enabling proactive remediation.
Network Security for Remote Access
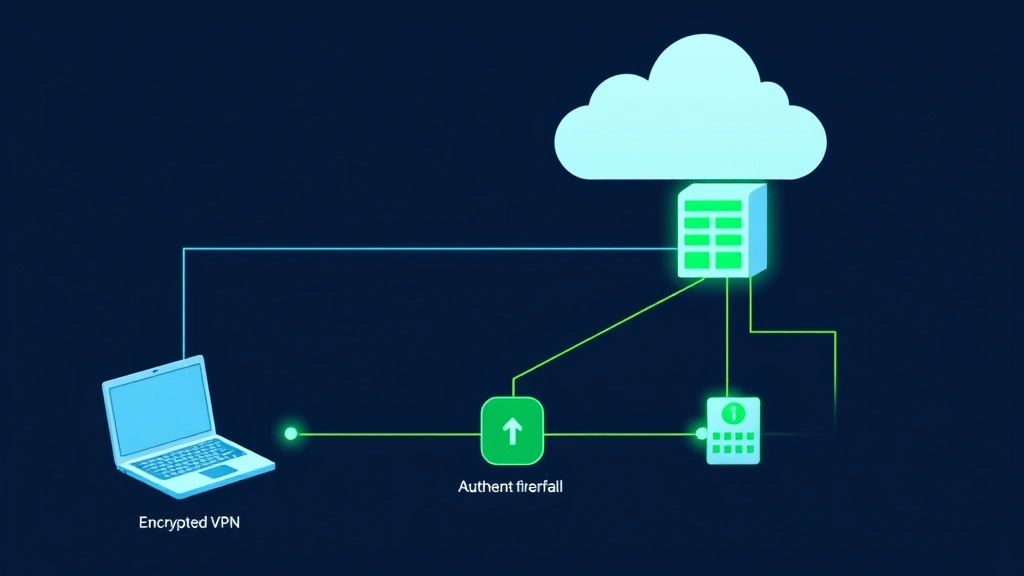
The network path between remote workers and virtual office login systems requires multiple layers of protection. Virtual Private Networks (VPNs) encrypt all traffic between user devices and corporate networks, preventing eavesdropping on public Wi-Fi networks. Zero Trust Network Access (ZTNA) solutions verify every access request regardless of network location, eliminating the implicit trust granted to users on corporate networks.
Network Security Components:
- VPN with strong encryption (AES-256 minimum) and perfect forward secrecy
- TLS 1.2+ for all login communications with HSTS headers
- Geofencing to block logins from unexpected geographic locations
- IP reputation filtering to block known malicious addresses
- Rate limiting on login endpoints to prevent brute force attacks
- DNS security to prevent DNS hijacking and pharming attacks
Certificate pinning prevents man-in-the-middle attacks by hardcoding expected SSL certificates within applications, making it impossible for attackers to intercept traffic even with compromised Certificate Authorities. Organizations implementing Admiral Security virtual office login systems should ensure all communications use modern TLS versions with strong cipher suites.
Endpoint security becomes critical when employees access virtual offices from personal devices. Mobile Device Management (MDM) solutions enforce security policies on company-issued and BYOD devices, ensuring devices maintain current patches, encryption, and security software before granting access.
Monitoring and Threat Detection
Proactive monitoring transforms login systems from static authentication mechanisms into dynamic security sensors. Behavioral analytics identify anomalous login patterns that may indicate compromised credentials, including unusual login times, geographic impossibilities, or access from unfamiliar devices.
Security Information and Event Management (SIEM) systems aggregate login logs from virtual office platforms, analyzing them for suspicious patterns. Alerts trigger when accounts attempt logins after hours, from multiple geographic locations within impossible timeframes, or using devices not previously associated with the account.
Key Monitoring Metrics:
- Failed login attempts per account and IP address
- Successful logins from new devices or locations
- Session duration anomalies
- Concurrent sessions from multiple locations
- Access to sensitive resources immediately after login
- Privilege escalation events following authentication
Threat intelligence feeds from security researchers and government agencies provide real-time information about emerging attack patterns. Organizations should subscribe to threat intelligence relevant to their industry and integrate findings into detection rules. The CISA Alerts and Advisories provide timely information about active exploitation campaigns.
Incident response procedures must define clear escalation paths when suspicious login activity is detected. Rapid response to compromised credentials—including forced password resets and session termination—prevents attackers from establishing persistent access.
Compliance and Security Standards
Virtual office login systems must align with relevant regulatory frameworks and security standards. HIPAA requires healthcare organizations to implement authentication controls protecting patient data. PCI DSS mandates strong authentication for systems accessing payment card information. GDPR requires organizations to implement appropriate technical measures protecting personal data of EU residents.
The NIST SP 800-171 Security Requirements for Controlled Unclassified Information provides comprehensive guidance for protecting sensitive information, including detailed authentication requirements. Organizations working with federal contractors must implement controls aligned with these standards.
SOC 2 Type II certifications demonstrate that service providers, including virtual office platforms, maintain rigorous security controls including authentication, access controls, and monitoring. When evaluating Admiral Security virtual office login systems or competing platforms, request SOC 2 reports confirming security control implementation.
Regular security audits and penetration testing validate that virtual office login systems resist real-world attack techniques. Third-party security assessments provide independent verification of security claims and identify vulnerabilities before threat actors discover them. Organizations should establish annual penetration testing schedules with qualified security firms.
Employee training remains a critical compliance requirement. Security awareness programs must educate remote workers about phishing threats, password security, and proper handling of credentials. Simulated phishing campaigns measure training effectiveness and identify employees requiring additional education.
Documentation of security controls, incident response procedures, and access logs demonstrates due diligence in security implementation. When regulatory investigations occur, comprehensive documentation proves that organizations implemented reasonable security measures consistent with industry standards.
The intersection of security and usability determines whether employees comply with security policies or circumvent them through convenience shortcuts. Well-designed authentication systems balance security with user experience, recognizing that overly burdensome processes encourage insecure workarounds.
FAQ
What makes Admiral Security virtual office login different from other platforms?
Admiral Security implements enterprise-grade authentication controls including mandatory MFA, advanced threat detection, and compliance certifications. However, the specific features depend on your organization’s deployment. Review your platform documentation and contact your administrator for detailed capability information.
How often should employees change virtual office passwords?
Modern security guidance recommends password changes only when compromise is suspected, rather than arbitrary periodic changes. However, if your organization maintains mandatory password expiration policies, quarterly changes for standard accounts and monthly changes for administrative accounts represent reasonable baselines.
Are biometric authentication methods secure for remote access?
Biometric authentication provides strong security when properly implemented, particularly when combined with additional factors. Ensure biometric systems use secure storage and transmission protocols. Biometric data cannot be changed like passwords if compromised, so consider whether your organization’s risk profile supports biometric authentication.
What should employees do if they suspect credential compromise?
Immediately change your password, enable MFA if not already active, review recent login activity, and notify your security team. Check Have I Been Pwned to determine if your credentials appear in known breaches. Monitor financial and credit accounts for suspicious activity.
How can organizations balance security with remote work productivity?
Implement single sign-on (SSO) solutions that authenticate once to access multiple applications, reducing login friction. Use device-based authentication for trusted company devices. Establish clear security policies and provide employees with tools supporting compliance. Regular communication about security importance helps employees understand why controls exist.
What role does encryption play in virtual office login security?
Encryption protects login credentials during transmission between user devices and authentication servers, preventing eavesdropping on public networks. End-to-end encryption ensures that only the intended recipient can decrypt sensitive authentication data. Always verify that virtual office platforms use strong encryption (AES-256 minimum) for all sensitive communications.


