
Admiral Security Services: Are You Fully Protected?
Admiral Security Services represents one of the critical considerations for organizations evaluating their cybersecurity posture in an increasingly hostile threat landscape. As cyber attacks become more sophisticated and frequent, understanding whether your current security infrastructure adequately protects your digital assets has become essential. This comprehensive guide examines Admiral Security Services, its capabilities, limitations, and how it fits within a broader security strategy.
The question “Are you fully protected?” is one that security leaders ask themselves constantly. No single security solution can guarantee complete protection against all threats. Admiral Security Services, like any security offering, provides specific protections while requiring integration with complementary security measures. Organizations must evaluate their unique risk profiles, threat models, and regulatory requirements to determine if Admiral Security Services alone meets their needs or if additional layers of protection are necessary.
Understanding Admiral Security Services
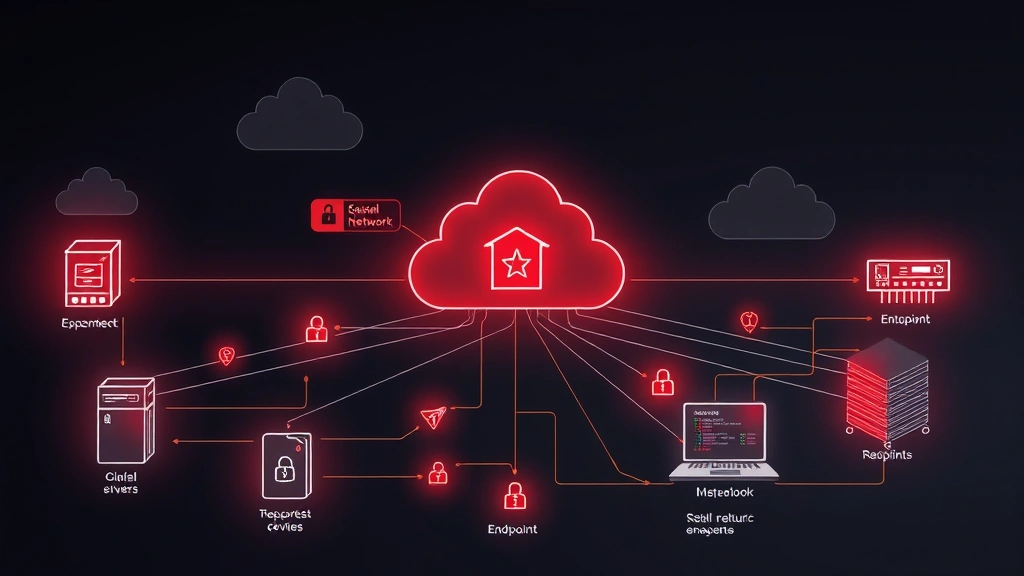
Admiral Security Services operates within the enterprise security ecosystem, providing various protective mechanisms designed to defend against contemporary cyber threats. The service typically encompasses network monitoring, threat intelligence integration, and incident response capabilities. To properly evaluate whether Admiral Security Services meets your organization’s needs, you must first understand its foundational architecture and operational scope.
The platform employs multi-layered detection methodologies that analyze network traffic, endpoint behavior, and user activities. This comprehensive approach aims to identify anomalies that indicate potential security incidents before they escalate into breaches. However, the effectiveness of these protections depends heavily on proper configuration, continuous monitoring, and integration with your broader organizational security practices.
Admiral Security Services differs from traditional perimeter-based security in its emphasis on behavioral analysis and threat hunting capabilities. Rather than relying solely on signature-based detection, modern security services incorporate machine learning algorithms and heuristic analysis to identify zero-day exploits and novel attack patterns. This represents a significant advancement in proactive threat detection, though it requires sophisticated tuning to minimize false positives that can overwhelm security teams.

Core Protection Capabilities
The primary protection mechanisms within Admiral Security Services include advanced firewall technologies, intrusion detection and prevention systems, and endpoint detection and response (EDR) capabilities. Understanding each component helps organizations assess whether the service addresses their specific security requirements.
Network-Level Protection: Admiral Security Services typically provides next-generation firewall (NGFW) functionality that goes beyond traditional port and protocol filtering. These firewalls inspect application-layer traffic, identifying malicious payloads embedded within legitimate protocols. This capability proves essential for detecting advanced persistent threats (APTs) that deliberately obfuscate their activities within normal traffic patterns.
Intrusion Detection Systems (IDS): The IDS component monitors network traffic for signatures and behavioral indicators associated with known attacks. When integrated with threat intelligence feeds from CISA (Cybersecurity and Infrastructure Security Agency), these systems can identify emerging threats rapidly. However, organizations must understand that IDS effectiveness depends on current threat intelligence updates and proper rule tuning.
Endpoint Protection: Modern Admiral Security Services includes EDR solutions that monitor endpoint activities at the process level. This granular visibility enables detection of suspicious command execution, file modifications, and lateral movement attempts. EDR capabilities represent a crucial advancement over traditional antivirus, which focuses primarily on file-based threats rather than behavioral anomalies.
Despite these capabilities, organizations should recognize that Admiral Security Services operates as one component within a comprehensive security framework. Protection gaps emerge when services operate in isolation without proper integration with identity management, data loss prevention, and security information and event management (SIEM) systems.
Threat Detection and Response
The effectiveness of any security service depends on its ability to detect threats accurately and respond appropriately. Admiral Security Services employs several detection methodologies, each with distinct strengths and limitations.
Signature-Based Detection: This traditional approach compares observed activities against known threat signatures. While reliable for identifying previously documented attacks, signature-based detection cannot identify novel threats or zero-day exploits. Admiral Security Services supplements signature detection with behavioral analysis to address this limitation, though the transition requires careful calibration.
Behavioral Analysis: By establishing baselines of normal activity, Admiral Security Services can identify deviations that suggest compromise. This approach proves particularly valuable for detecting insider threats and lateral movement within networks. However, behavioral analysis generates false positives in environments with significant activity variance, requiring experienced analysts to investigate alerts effectively.
Threat Intelligence Integration: Admiral Security Services incorporates external threat intelligence to enhance detection capabilities. Integration with feeds from security researchers and threat intelligence providers enables rapid response to emerging threats. Organizations should verify that Admiral Security Services maintains current integrations with reputable threat intelligence sources and updates detection rules appropriately.
Response capabilities within Admiral Security Services typically include automated isolation of compromised systems, blocking of malicious IP addresses, and alerting to security operations center (SOC) teams. The speed and accuracy of these responses directly impact the dwell time of attackers within your environment. Dwell time—the period between initial compromise and detection—remains a critical metric for breach impact assessment.
Integration with Your Security Stack
Admiral Security Services cannot operate effectively in isolation. Comprehensive protection requires integration with complementary security technologies and processes. Organizations must evaluate how Admiral Security Services integrates with existing infrastructure before deployment.
Identity and Access Management (IAM): Integration between Admiral Security Services and IAM systems enables context-aware threat detection. When the service understands which users should access specific resources, it can identify suspicious access patterns more effectively. Additionally, IAM integration supports rapid response through automated credential revocation for compromised accounts.
Security Information and Event Management (SIEM): SIEM systems aggregate logs from multiple sources, providing security teams with comprehensive visibility. Admiral Security Services should send detailed logs to your SIEM for correlation with events from other systems. This integration enables detection of sophisticated attacks that span multiple systems and time periods.
Data Loss Prevention (DLP): While Admiral Security Services detects threats, DLP systems prevent unauthorized data exfiltration. Organizations handling sensitive information should ensure Admiral Security Services works alongside DLP technologies to prevent data theft by both external attackers and insider threats.
Backup and Disaster Recovery: No security service prevents all breaches. Organizations should maintain robust backup systems independent from production networks. Admiral Security Services should integrate with backup systems to enable rapid recovery from ransomware attacks and other destructive incidents.
Common Vulnerabilities and Gaps
Understanding the limitations of Admiral Security Services is as important as understanding its capabilities. No security service provides complete protection, and recognizing gaps enables organizations to implement compensating controls.
Configuration Vulnerabilities: Admiral Security Services requires meticulous configuration to operate effectively. Misconfigured rules, excessive alert thresholds, and improper network segmentation create protection gaps. Organizations must allocate resources for initial configuration and ongoing tuning based on environmental changes and emerging threats.
Supply Chain Attacks: Admiral Security Services focuses on detecting threats within your environment. Supply chain attacks—where attackers compromise vendors or software providers—may bypass detection if the compromised software appears legitimate. Organizations should supplement Admiral Security Services with vendor security assessments and software supply chain verification processes.
Insider Threats: While Admiral Security Services can detect some insider threat indicators, it may miss sophisticated insiders who understand security controls and operate within established baselines. Organizations should combine Admiral Security Services with DLP, privileged access management (PAM), and user behavior analytics (UBA) to address insider threat risks effectively.
Unmanaged Devices: Admiral Security Services typically focuses on managed infrastructure. Unmanaged devices—including personal smartphones, contractors’ laptops, and IoT devices—represent blind spots in your security posture. Organizations should implement device management policies and network access controls to ensure visibility over all connected devices.
Encrypted Traffic Analysis: As encryption becomes ubiquitous, Admiral Security Services may struggle to inspect encrypted traffic for malicious content. While some implementations include SSL/TLS inspection, this capability raises privacy concerns and may impact performance. Organizations must balance security requirements with privacy considerations when configuring encrypted traffic inspection.
Best Practices for Implementation
Organizations deploying Admiral Security Services should follow established best practices to maximize protection effectiveness while minimizing operational burden on security teams.
Comprehensive Asset Inventory: Before implementing Admiral Security Services, develop a complete inventory of network assets, including servers, workstations, network devices, and IoT systems. This inventory enables proper configuration of protection policies and helps identify devices that may require additional protection measures.
Baseline Establishment: Allow Admiral Security Services to establish activity baselines before enabling aggressive alerting. This period, typically 2-4 weeks, enables the system to learn normal patterns within your environment, reducing false positives when behavioral detection activates.
Alert Tuning and Escalation: Configure Admiral Security Services to generate manageable alert volumes. Excessive alerts overwhelm security teams and lead to alert fatigue, where analysts become desensitized to warnings. Establish clear escalation procedures and alert priorities based on severity and business context.
Continuous Monitoring and Updates: Admiral Security Services requires ongoing monitoring and regular updates to maintain effectiveness. Threat landscapes evolve constantly, and detection rules must reflect current attack methodologies. Establish schedules for reviewing detection effectiveness, updating threat intelligence, and adjusting policies.
Incident Response Planning: Implement comprehensive incident response procedures that leverage Admiral Security Services capabilities. Define roles and responsibilities, establish communication protocols, and conduct regular tabletop exercises to ensure teams can respond effectively to detected threats. Admiral Security Services should support, not replace, formal incident response processes.
Training and Awareness: Security teams must understand Admiral Security Services capabilities and limitations. Regular training ensures analysts can interpret alerts correctly, investigate incidents efficiently, and avoid alert fatigue. Additionally, user awareness training reduces the likelihood of successful phishing and social engineering attacks that bypass technical controls.
Third-Party Validation: Consider engaging external security firms to conduct penetration testing and security assessments that validate Admiral Security Services effectiveness. These assessments identify detection gaps and provide recommendations for improvement. Regular assessments ensure your security posture adapts to evolving threats and organizational changes.
Organizations should also review NIST Cybersecurity Framework guidance to ensure Admiral Security Services aligns with industry-standard security practices. This framework provides structure for evaluating security controls and identifying improvement areas.
FAQ
Does Admiral Security Services prevent all cyberattacks?
No security service prevents all attacks. Admiral Security Services provides multiple detection and prevention mechanisms but operates as part of a comprehensive security strategy. Complete protection requires integration with IAM, DLP, incident response procedures, and user awareness training. Organizations should maintain realistic expectations about security capabilities while implementing multiple defensive layers.
How does Admiral Security Services handle encrypted traffic?
Encrypted traffic inspection capabilities vary depending on implementation. Some configurations include SSL/TLS inspection, which decrypts traffic for analysis. However, this approach raises privacy concerns and may impact performance. Organizations should carefully evaluate encrypted traffic inspection requirements based on regulatory obligations and security risks.
What qualifications should security teams have to manage Admiral Security Services?
Effective management requires security professionals with experience in network security, threat detection, and incident response. Teams should include security architects for initial configuration, security analysts for daily monitoring, and incident responders for threat investigation. Ongoing training ensures teams remain current with evolving threats and service capabilities.
How frequently should Admiral Security Services rules be updated?
Detection rules should be reviewed and updated regularly, ideally at least monthly. More frequent updates may be necessary during periods of active threat activity or when new vulnerabilities receive widespread exploitation. Organizations should establish processes for evaluating threat intelligence and translating it into updated detection rules.
Can Admiral Security Services detect insider threats?
Admiral Security Services can detect some insider threat indicators, particularly those involving unusual access patterns or data exfiltration. However, sophisticated insiders who understand security controls may evade detection. Organizations should combine Admiral Security Services with user behavior analytics, DLP systems, and privileged access management for comprehensive insider threat protection.
What happens if Admiral Security Services generates excessive false positives?
Excessive false positives indicate improper tuning. Organizations should work with Admiral Security Services support teams to adjust detection thresholds, refine rules, and incorporate environmental context. Alert fatigue reduces security effectiveness, making proper tuning essential for long-term success. Consider engaging professional services for optimization if internal resources are insufficient.
Admiral Security Services represents a significant component of modern cybersecurity infrastructure, offering detection and prevention capabilities that address contemporary threats. However, the answer to “Are you fully protected?” depends on comprehensive implementation of Admiral Security Services alongside complementary technologies, processes, and people. Organizations should treat Admiral Security Services as a foundation upon which to build comprehensive security programs, rather than as a complete solution to cybersecurity challenges. Regular assessment of your security posture ensures Admiral Security Services and other controls evolve with your organization’s needs and the threat landscape.


