
AAA Smart Home Security: Expert Guide to Safeguarding Your Connected Home
Smart home technology has revolutionized how we live, offering unprecedented convenience through connected devices, automated systems, and remote control capabilities. However, this interconnected ecosystem introduces significant cybersecurity vulnerabilities that homeowners must address. AAA Smart Home Security encompasses a comprehensive approach to protecting your connected devices, personal data, and physical safety from evolving cyber threats. As more households embrace smart speakers, security cameras, smart locks, and IoT devices, understanding the security landscape becomes essential for maintaining a truly protected home environment.
The intersection of convenience and security creates a delicate balance that many homeowners overlook. Inadequately secured smart home systems can expose sensitive information, enable unauthorized access to your residence, and compromise your family’s privacy. This expert guide explores the critical aspects of AAA Smart Home Security, providing actionable strategies to fortify your connected home against sophisticated cyber attacks and unauthorized access attempts.

Understanding Smart Home Security Fundamentals
Smart home security operates on three foundational pillars: device security, network security, and user behavior. Each component plays a critical role in the overall protection framework. According to CISA (Cybersecurity and Infrastructure Security Agency), securing IoT devices requires understanding their vulnerabilities and implementing layered defense mechanisms. Most smart home breaches occur due to weak passwords, unpatched firmware, and inadequate network segmentation.
The attack surface of a modern smart home extends far beyond traditional computers. Smart speakers, thermostats, doorbell cameras, lighting systems, and refrigerators all represent potential entry points for cybercriminals. When these devices connect to your home network without proper security protocols, they create pathways for attackers to access sensitive information, including banking details, health records, and location data. Understanding this interconnected vulnerability landscape is the first step toward implementing effective AAA Smart Home Security measures.
The threat landscape continues evolving as attackers develop sophisticated techniques to exploit smart home ecosystems. Botnets specifically designed to target IoT devices have infected millions of homes worldwide, turning innocent smart devices into weapons for launching distributed denial-of-service attacks. By comprehending these fundamental threats, homeowners can make informed decisions about device selection, network architecture, and security practices.
Device-Level Security Measures
Securing individual smart home devices represents the foundation of comprehensive protection. Each device requires individual attention regarding authentication, encryption, and firmware management. When purchasing smart home technology, prioritize manufacturers with strong security track records and transparent vulnerability disclosure policies. Research vendors who regularly release security patches and maintain active support for their products.
Firmware updates represent one of the most critical yet frequently neglected security practices. Manufacturers release updates to patch discovered vulnerabilities, enhance encryption protocols, and improve authentication mechanisms. Enabling automatic updates on all smart home devices ensures you receive security patches promptly. Many modern smart home devices offer automatic update functionality—activate this feature immediately upon installation. NIST guidelines for IoT security emphasize firmware management as a cornerstone of device-level protection.
Default credentials pose an enormous security risk in smart home environments. Manufacturers often ship devices with standard usernames and passwords that remain unchanged across thousands of units. Attackers maintain databases of default credentials and systematically attempt to access exposed devices. Immediately change all default passwords to strong, unique credentials upon device setup. Implement a password manager to track complex passwords across your growing inventory of connected devices.
Consider implementing device isolation through network segmentation, which we’ll explore further in the network protection section. Additionally, disable unnecessary features and services on smart devices. Many devices include remote access capabilities, cloud connectivity, and data collection features that aren’t essential for basic functionality. Disabling unused features reduces your attack surface significantly.
Encryption protocols vary significantly across smart home devices. Prioritize devices that support WPA3 wireless encryption, TLS 1.2 or higher for data transmission, and end-to-end encryption for sensitive communications. Some smart speakers and security cameras offer optional encryption features—enable these protections even if they slightly impact convenience.
Network Protection Strategies
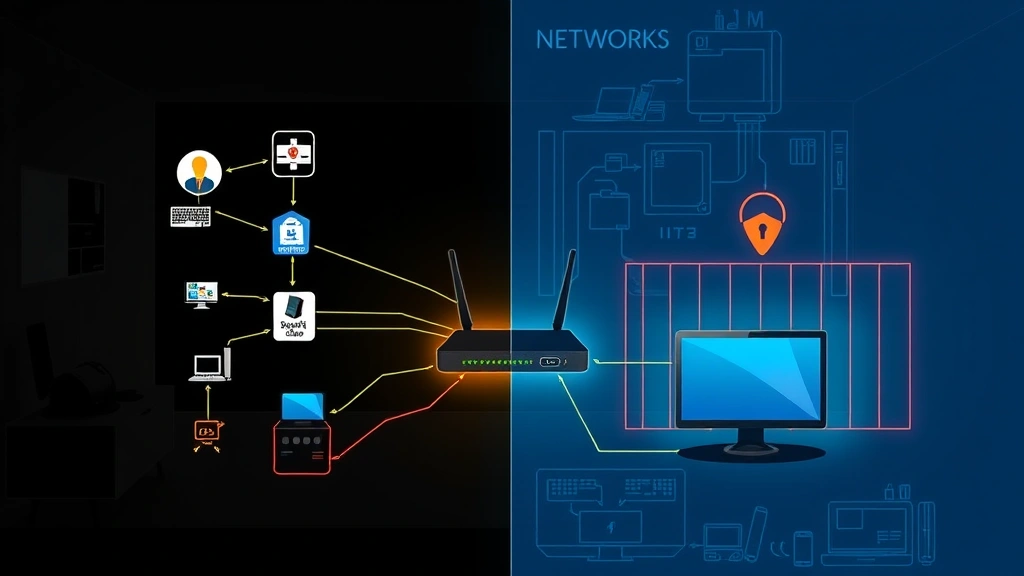
Your home network serves as the backbone of AAA Smart Home Security. A compromised network can expose all connected devices to attackers, regardless of individual device security measures. Implementing robust network-level protections creates a secure foundation for all smart home systems.
Network segmentation represents one of the most effective protection strategies available to homeowners. This technique involves creating separate network segments for different device categories. Establish a dedicated IoT network for smart home devices, separate from networks hosting computers, smartphones, and sensitive systems. Modern routers increasingly offer native support for network segmentation through virtual LANs or guest networks. This isolation prevents compromised IoT devices from accessing your personal computers or sensitive data stored on other devices.
Your wireless router requires the same security attention as individual devices. Change default administrative credentials immediately, update router firmware regularly, and enable the strongest available encryption standard (WPA3, or WPA2 if WPA3 isn’t available). Disable WPS (Wi-Fi Protected Setup), which introduces security vulnerabilities. Configure your router to hide SSID broadcast if desired, though this provides minimal security benefit compared to strong encryption.
Implement a robust firewall configuration on your router and consider enabling intrusion detection capabilities if available. Many modern routers include basic intrusion detection and prevention features that monitor for suspicious network activity. These tools can alert you to potential attacks or compromised devices attempting unusual network behavior.
Consider deploying a dedicated network security appliance for enhanced monitoring and protection. Devices like Firewalla or similar home network security solutions provide advanced threat detection, malware blocking, and detailed network analytics. These systems monitor all network traffic flowing through your home, identifying suspicious patterns and blocking known malicious domains.
DNS security offers another critical network protection layer. Change your router’s DNS settings from default ISP-provided servers to security-focused alternatives like Cloudflare’s 1.1.1.1 for Families or Quad9, which filter malicious domains and prevent access to known phishing sites. This protection applies to all connected devices on your network, providing comprehensive filtering without requiring individual device configuration.
Authentication and Access Control
Strong authentication mechanisms prevent unauthorized access to your smart home systems and personal data. Moving beyond basic password protection creates multiple security barriers that significantly increase attacker effort.
Multi-factor authentication (MFA) should be enabled on all smart home accounts, including cloud services associated with your devices. MFA requires a second verification factor beyond passwords—typically a code generated by an authenticator app, SMS message, or hardware security key. While SMS-based MFA has known vulnerabilities, it still provides substantial protection compared to password-only access. Authenticator apps like Google Authenticator or Authy offer superior security to SMS alternatives.
Create strong, unique passwords for each smart home device and associated cloud accounts. Avoid common patterns, dictionary words, or personal information that attackers might guess. Passwords should exceed 16 characters and combine uppercase letters, lowercase letters, numbers, and special characters. Password managers like Bitwarden, 1Password, or KeePass simplify managing complex credentials across your expanding smart home ecosystem.
Review and restrict access permissions on cloud-based smart home services. Many platforms allow sharing access with family members—ensure only necessary individuals have access and regularly audit who maintains active access. Some services offer granular permission controls allowing you to restrict specific features or devices to particular users. Implement these restrictions to minimize exposure if a family member’s account becomes compromised.
Biometric authentication options available on some smart devices (fingerprint, facial recognition) provide convenience without sacrificing security. However, these systems vary in implementation quality. Research biometric security implementations before relying on them as primary authentication methods. Biometric data stored locally on devices offers better privacy protection than biometric data transmitted to cloud servers.
Privacy Protection in Connected Homes
Smart home security extends beyond preventing unauthorized access to encompassing privacy protection from manufacturers and data collectors. Many smart home devices continuously collect data about your behavior, preferences, and routines. Understanding and controlling this data collection is essential for comprehensive privacy protection.
Review privacy policies for all smart home devices and associated services. These documents detail what data manufacturers collect, how they use information, and whether they share data with third parties. While reading lengthy privacy policies proves tedious, critical sections address data retention periods, third-party sharing, and user rights regarding data deletion. Some manufacturers offer privacy-focused modes that disable certain data collection features—activate these options if available.
Smart speakers and always-on microphones deserve particular privacy scrutiny. These devices continuously listen for wake words, requiring local processing of audio data. Understand exactly what audio data is recorded, transmitted to cloud servers, and retained. Many manufacturers retain audio recordings indefinitely unless explicitly deleted. Disable cloud-based features if you’re uncomfortable with this data collection, or physically mute microphones when privacy is paramount.
Video surveillance devices including doorbell cameras and security cameras raise significant privacy concerns. Ensure video feeds are encrypted during transmission and storage. Review cloud storage practices—some services retain footage indefinitely while others limit retention periods. Configure strict access controls limiting who can view recorded footage. If possible, implement local storage solutions that keep video data on your home network rather than relying on cloud services.
Consider implementing a home VPN (Virtual Private Network) for additional privacy protection. A home VPN encrypts all network traffic leaving your residence, preventing ISPs and network eavesdroppers from monitoring your online activities. This provides protection for all connected devices without requiring individual configuration. However, home VPN implementation requires technical expertise and specific router capabilities.
Monitoring and Incident Response
Proactive monitoring enables early detection of security incidents before attackers cause significant damage. Implementing effective monitoring practices and developing incident response procedures completes your AAA Smart Home Security framework.
Monitor your network for unusual activity indicating potential compromises. Most routers provide access logs showing connected devices and network traffic patterns. Regularly review these logs for unfamiliar devices, unusual bandwidth consumption, or unexpected connection attempts. Many network security appliances provide automated alerts when suspicious activity occurs, enabling rapid response.
Implement regular security audits of your smart home ecosystem. Periodically review connected devices, access permissions, firmware versions, and security settings. Create a detailed inventory of all smart home devices including models, firmware versions, and last update dates. This documentation facilitates security management and helps identify devices requiring urgent updates.
Establish clear incident response procedures for suspected security breaches. If you suspect a smart home device compromise, immediately isolate the affected device from your network, change associated account passwords, and contact the manufacturer. Review account activity logs for unauthorized access and monitor financial accounts for fraudulent transactions. Document all incident details for reference and potential law enforcement reporting.
Stay informed about emerging threats affecting smart home devices. Security researchers regularly discover vulnerabilities in popular smart home platforms and devices. Subscribe to security mailing lists, follow reputable cybersecurity news sources, and monitor manufacturer security bulletins. Security research communities provide valuable threat intelligence about newly discovered vulnerabilities before mainstream media coverage.
Consider cyber insurance policies that cover smart home-related incidents. Some homeowners insurance policies include cyber liability coverage, though specific coverage varies significantly. Review your existing policies and consider dedicated cyber insurance if available in your region. Understanding your coverage helps inform security investment decisions.
Educate household members about smart home security practices. Ensure family members understand the importance of strong passwords, the dangers of public Wi-Fi, and proper device handling. Security awareness training makes every household member a security contributor rather than a potential vulnerability. Regular reminders about best practices maintain security focus as new devices join your ecosystem.
FAQ
What is AAA Smart Home Security?
AAA Smart Home Security refers to a comprehensive, multi-layered approach to protecting connected home devices, networks, and personal data from cyber threats. It encompasses device-level security, network protection, authentication mechanisms, privacy controls, and incident monitoring to create a secure smart home ecosystem.
How often should I update smart home device firmware?
Enable automatic firmware updates on all smart home devices to receive security patches immediately upon release. If automatic updates aren’t available, manually check for updates monthly. Critical security patches should be installed within days of release, as attackers often develop exploits for newly disclosed vulnerabilities.
Is network segmentation necessary for smart home security?
Network segmentation significantly improves security by isolating IoT devices from computers and sensitive systems. While not absolutely required, segmentation prevents compromised smart devices from accessing personal computers or sensitive data. Most modern routers support network segmentation through guest networks or virtual LANs, making implementation straightforward.
What password length is sufficient for smart home devices?
Aim for passwords exceeding 16 characters combining uppercase letters, lowercase letters, numbers, and special characters. Longer passwords exponentially increase the time required for brute-force attacks to succeed. Avoid dictionary words, common patterns, or personal information that attackers might guess through social engineering.
Should I disable smart home devices I don’t actively use?
Yes, disabling unused devices reduces your attack surface. If you’re not actively using a smart device, either power it off, disconnect it from your network, or consider removing it entirely. Unused devices still require security updates and monitoring, creating unnecessary security burden without providing benefits.
How do I know if my smart home has been compromised?
Signs of compromise include unusual network activity, devices behaving unexpectedly, unfamiliar accounts accessing your services, unexpected cloud storage usage, or strangers appearing in security camera footage. Monitor your router’s connected device list, review account activity logs, and track bandwidth consumption for anomalies. Network monitoring tools can automatically alert you to suspicious activity patterns.
What should I do if I discover a compromised smart device?
Immediately isolate the device from your network, change associated account passwords, review account activity for unauthorized access, and contact the manufacturer. Check your router logs for other unusual activity, monitor financial accounts for fraud, and consider resetting your router if you suspect network-wide compromise. Document all incident details for potential law enforcement reporting.
Are smart home security systems vulnerable to hacking?
Yes, smart home security systems face the same vulnerabilities as other IoT devices. Weak passwords, unpatched firmware, and insecure network configurations create entry points for attackers. However, implementing the AAA Smart Home Security practices outlined in this guide substantially reduces vulnerability to common attack vectors.
Can I use the same password across multiple smart home devices?
No, using identical passwords across multiple devices creates cascading compromise risk. If attackers access one device’s credentials, they can immediately access all systems using the same password. Password managers simplify managing unique passwords across your smart home ecosystem without requiring manual memorization.


