
Is Your Cybersecurity Strategy Bulletproof? Expert Insights
In an era where cyber threats evolve faster than organizations can defend against them, the question isn’t whether your business will face a security incident—it’s when. Modern cybersecurity demands more than reactive measures and outdated protocols. It requires a comprehensive, multi-layered defense strategy that anticipates threats, responds swiftly, and continuously adapts to emerging vulnerabilities. Whether you’re protecting critical infrastructure, managing sensitive customer data, or safeguarding intellectual property, understanding what makes a cybersecurity strategy truly bulletproof has become essential for organizational survival and reputation.
The landscape of digital threats has transformed dramatically over the past decade. From ransomware attacks that cripple entire enterprises to sophisticated supply chain compromises that bypass traditional security perimeters, adversaries are employing increasingly advanced techniques. Organizations must therefore implement defense mechanisms that go beyond simple firewalls and antivirus software. A bulletproof cybersecurity strategy integrates people, processes, and technology into a cohesive framework designed to detect, prevent, and respond to threats at every level.

Understanding the Modern Threat Landscape
Cybersecurity threats have evolved from simple viruses to sophisticated, coordinated attacks involving multiple threat actors and advanced persistent techniques. According to the Cybersecurity and Infrastructure Security Agency (CISA), the threat landscape continues to expand with state-sponsored actors, organized cybercriminal groups, and opportunistic attackers all competing in the digital space. Understanding these threats is the foundation of any effective security strategy.
Organizations face threats ranging from external attacks to internal negligence. Ransomware campaigns specifically target high-value assets, exploiting vulnerabilities in systems that haven’t been properly patched or monitored. Phishing attacks remain the most effective entry vector, with attackers using sophisticated social engineering to bypass technical controls. Supply chain attacks represent another critical concern, where attackers infiltrate trusted vendors to gain access to multiple downstream targets. Data exfiltration, credential theft, and business email compromise continue to plague organizations across every industry sector.
The sophistication of attacks has increased proportionally with the expansion of attack surface areas. Cloud migrations, remote work environments, and interconnected IoT devices have created new vulnerabilities that traditional security models weren’t designed to address. Organizations must therefore understand not just what threats exist, but how they evolve and adapt to circumvent existing defenses.
Core Components of Bulletproof Cybersecurity
A truly bulletproof cybersecurity strategy rests on several foundational pillars that work in concert to provide comprehensive protection. These components address different aspects of security and together create a resilient defense posture.
Asset Inventory and Management forms the essential first step. You cannot protect what you don’t know exists. Organizations must maintain a comprehensive inventory of all hardware, software, cloud resources, and data assets. This includes identifying shadow IT—unauthorized systems and applications that exist outside official channels but contain valuable or sensitive information. Regular asset audits ensure nothing falls through the cracks.
Vulnerability Management involves continuous identification, prioritization, and remediation of security weaknesses. This process includes regular vulnerability scanning, penetration testing, and security assessments. Organizations should prioritize patching critical vulnerabilities that are actively exploited in the wild while maintaining a disciplined schedule for routine updates. A vulnerability management program should integrate with incident response procedures to address zero-day exploits swiftly.
Access Control and Identity Management ensure that only authorized individuals can access specific resources. Implementing the principle of least privilege—granting users only the minimum access necessary for their role—significantly reduces attack surface. Multi-factor authentication adds an additional security layer, making credential theft less devastating. Regular access reviews should remove unnecessary permissions and identify anomalous access patterns.
Network Segmentation divides your network into distinct zones, limiting lateral movement if one segment is compromised. Critical systems should be isolated from general network traffic, and sensitive data should reside in protected enclaves. This approach prevents attackers from pivoting across your entire infrastructure after gaining initial access.
Monitoring and Detection capabilities provide the eyes and ears of your security operation. Security Information and Event Management (SIEM) systems aggregate logs from across your infrastructure, enabling threat detection. Endpoint Detection and Response (EDR) tools monitor individual devices for suspicious behavior. Network monitoring identifies unusual traffic patterns and potential command-and-control communications. These detection systems should integrate with alerting mechanisms that enable rapid human response.
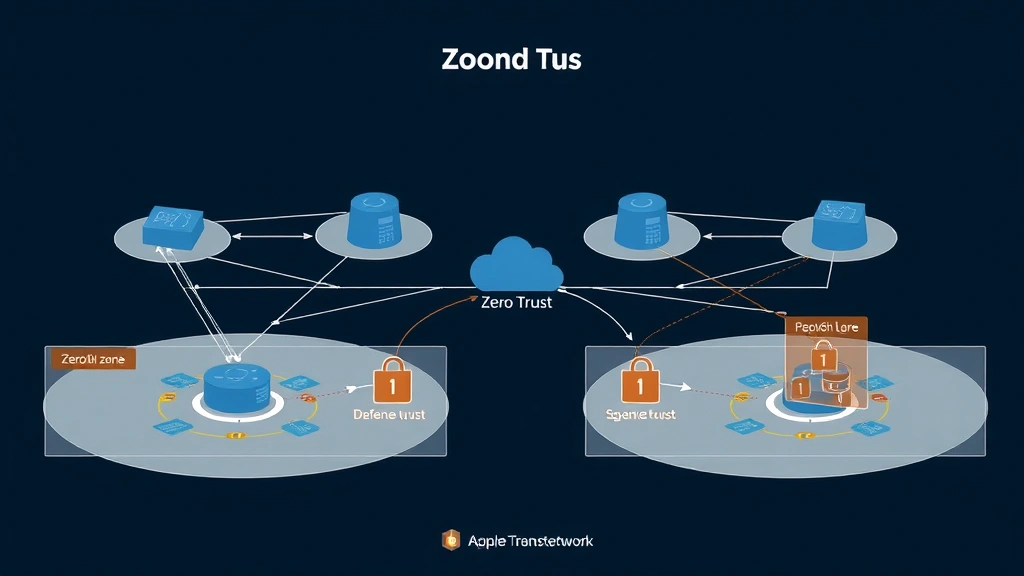
Zero Trust Architecture and Implementation
Zero Trust represents a paradigm shift in how organizations approach security. Rather than assuming that anything inside the network perimeter is trustworthy, Zero Trust requires verification of every access request, regardless of origin or destination. This model acknowledges that modern networks lack a clear perimeter—with cloud services, remote workers, and third-party integrations, the traditional castle-and-moat approach has become obsolete.
NIST’s Zero Trust Architecture guidelines provide a framework for implementing this model. The approach requires continuous authentication and authorization, encryption of all traffic, and microsegmentation of networks. Every device must be verified before connecting, every user must authenticate with strong credentials, and every application access must be logged and monitored.
Implementing Zero Trust architecture involves several key steps. First, establish detailed asset and data inventory to understand what needs protection. Second, implement strong identity verification mechanisms including multi-factor authentication across all systems. Third, deploy microsegmentation to create granular access controls. Fourth, encrypt data both in transit and at rest. Finally, implement comprehensive logging and monitoring to detect any policy violations or suspicious behavior.
Organizations transitioning to Zero Trust should adopt a phased approach, starting with critical systems and expanding gradually. This allows teams to develop expertise while minimizing disruption to business operations. Pilot programs in specific departments or business units can validate the approach before enterprise-wide rollout.
Building a Security-First Culture
Technology alone cannot create a bulletproof cybersecurity strategy. The human element remains both the greatest vulnerability and the strongest asset. Organizations must cultivate a security-first culture where every employee understands their role in protecting the organization.
Security awareness training should be continuous and role-specific. General awareness programs educate all employees about phishing, social engineering, and password hygiene. Specialized training for developers teaches secure coding practices. Training for system administrators focuses on secure configuration and access management. Executive training ensures leadership understands cyber risks and allocates appropriate resources.
Phishing simulations provide practical training that tests employee responses to realistic threats. Organizations should track metrics on click rates, report rates, and repetition patterns to identify employees needing additional training. Importantly, the goal should be educational rather than punitive—employees who report phishing attempts should be recognized and rewarded, not penalized.
Incident reporting mechanisms must be easily accessible and non-punitive. Employees who discover security issues should feel empowered to report them without fear of blame. Creating psychological safety around security enables early detection of problems before they escalate into major breaches. Organizations should establish clear escalation procedures and ensure that security concerns receive prompt attention.
Leadership commitment to security sets the tone for the entire organization. When executives prioritize cybersecurity investments, allocate budget appropriately, and model secure behaviors, employees follow suit. Security should be integrated into business decision-making rather than treated as an IT afterthought.
Incident Response and Business Continuity
Despite best prevention efforts, security incidents will occur. Organizations must prepare for this inevitability with well-designed incident response plans and business continuity strategies. Incident response speed significantly impacts breach impact—organizations that detect and contain incidents quickly minimize data loss and operational disruption.
An effective incident response plan includes clear definitions of incident severity levels, defined roles and responsibilities, communication protocols, and documented procedures for different incident types. The plan should specify who has authority to declare an incident, who must be notified, and what immediate actions should be taken. Regular tabletop exercises and simulations ensure teams can execute the plan effectively under pressure.
The incident response process typically follows four phases: preparation, detection and analysis, containment and eradication, and recovery. During preparation, organizations establish tools, processes, and trained personnel. Detection and analysis involves identifying and understanding the incident. Containment and eradication stops the attack and removes attacker access. Recovery restores systems to normal operations and implements improvements to prevent recurrence.
Business continuity planning ensures that critical functions can continue despite disruptions. This includes identifying critical business processes, determining recovery time objectives (RTO) and recovery point objectives (RPO), and establishing backup systems. Regular testing of backup and recovery procedures validates that your organization can actually restore operations when needed.
Post-incident activities are equally important. Organizations should conduct thorough investigations to understand how the incident occurred, document lessons learned, and implement improvements to prevent similar incidents. Threat intelligence gathered during incident response should inform security improvements across the organization.
Compliance and Regulatory Frameworks
Regulatory compliance provides another important dimension of cybersecurity strategy. Frameworks like HIPAA, PCI-DSS, GDPR, and SOC 2 establish minimum security requirements that organizations must meet. While compliance doesn’t guarantee security, these frameworks provide structured guidance on implementing effective controls.
Organizations should map their security program against applicable regulatory requirements and industry standards. The NIST Cybersecurity Framework provides a comprehensive structure for organizing security activities around five core functions: Identify, Protect, Detect, Respond, and Recover. This framework applies regardless of industry and helps organizations assess their security posture systematically.
Regular compliance audits and assessments identify gaps between current practices and required standards. Third-party auditors can provide independent validation of your security program and identify areas needing improvement. Documentation of controls, policies, and procedures supports both compliance and internal security management.
Compliance activities should integrate with security operations rather than existing as separate functions. Security controls implemented to meet regulatory requirements strengthen overall security posture. Organizations that view compliance as a minimum baseline and strive for security excellence beyond compliance requirements build stronger defenses.
Emerging Technologies in Defense
Emerging technologies offer promising capabilities for enhancing cybersecurity defenses. Artificial intelligence and machine learning enable more sophisticated threat detection by identifying patterns that human analysts might miss. These technologies can analyze vast quantities of security data to spot anomalies, predict attacks, and automate response actions.
Behavioral analytics monitor user and entity behavior to identify compromised accounts or insider threats. By establishing baselines of normal behavior, these systems detect deviations that might indicate unauthorized access or malicious activity. This approach catches sophisticated attackers who might evade signature-based detection.
Automated response capabilities enable faster incident containment. Security orchestration, automation, and response (SOAR) platforms coordinate across multiple security tools, enabling rapid response to detected threats. Automated playbooks can isolate compromised systems, disable accounts, or block malicious traffic before human intervention is required.
Quantum computing represents both opportunity and threat. While quantum computers could eventually break current encryption algorithms, organizations can prepare by transitioning to quantum-resistant cryptography. NIST’s Post-Quantum Cryptography project is developing standards for encryption methods that will resist quantum-level attacks.
Threat intelligence sharing platforms enable organizations to benefit from collective knowledge about emerging threats. Participating in information sharing communities provides early warning about attacks targeting your industry and helps coordinate defensive responses. Organizations should balance the value of threat intelligence with appropriate confidentiality protections for sensitive information.
FAQ
What is the most critical component of a bulletproof cybersecurity strategy?
While all components are important, strong access controls combined with continuous monitoring provide the foundation for effective defense. If attackers cannot easily gain access and cannot operate undetected, the probability of successful attacks decreases significantly. However, true resilience requires all components working together—technical controls must be supported by strong policies, trained personnel, and incident response capabilities.
How often should organizations assess their cybersecurity posture?
Assessments should occur at least annually as part of formal security reviews, but continuous monitoring and periodic testing should happen more frequently. Vulnerability scans should run weekly or more often. Penetration testing should occur at least annually, with more frequent testing for high-risk assets. Incident response drills should occur quarterly. This layered approach to assessment ensures that security gaps are identified and addressed promptly.
Can small organizations implement bulletproof cybersecurity strategies?
Absolutely. While large organizations may have more resources, small organizations can implement effective security by focusing on fundamentals. Prioritizing critical assets, implementing strong access controls, maintaining current patches, monitoring for threats, and preparing for incidents provides solid protection regardless of organization size. Cloud-based security services enable smaller organizations to access enterprise-grade tools without massive capital investment.
How does armed security employment relate to cybersecurity strategy?
Physical security and cybersecurity are interconnected. Armed security personnel protect physical infrastructure that houses critical systems, preventing unauthorized physical access to servers, network equipment, and sensitive areas. While armed security employment focuses on physical threats, it complements cybersecurity by preventing attackers from using physical access to compromise systems or steal hardware containing sensitive data. A comprehensive security strategy addresses both physical and cyber threats.
What should organizations do if they discover a security breach?
Organizations should immediately activate their incident response plan. Initial steps include isolating affected systems to prevent further compromise, notifying the incident response team, and beginning investigation to determine breach scope. Depending on applicable regulations and breach type, organizations may need to notify customers, regulators, and law enforcement. Throughout the process, preserve evidence for investigation and maintain detailed records of actions taken.
How can organizations stay current with evolving threats?
Subscribe to threat intelligence feeds and advisories from organizations like CISA. Participate in industry information sharing groups. Follow security researchers and organizations tracking emerging threats. Attend security conferences and training events. Maintain relationships with security consultants who track threat landscape changes. Importantly, establish processes to translate threat intelligence into security improvements—awareness without action provides no benefit.


