
Is Your AIM Security Updated? Expert Checklist for Maximum Protection
AIM (AOL Instant Messenger) security remains a critical concern for organizations and individuals still utilizing legacy communication systems. While AIM officially ceased operations in 2017, many enterprises continue running instances of this protocol within their infrastructure, creating significant security vulnerabilities if not properly maintained. Understanding whether your AIM security is updated requires a comprehensive approach that addresses authentication mechanisms, encryption standards, access controls, and threat mitigation strategies.
This expert checklist provides security professionals and system administrators with actionable guidance to assess and strengthen AIM security postures. Whether you’re managing legacy systems or migrating away from AIM entirely, following these verification steps ensures your communication infrastructure meets modern cybersecurity standards and protects sensitive organizational data from unauthorized access and interception.
Understanding AIM Security Vulnerabilities
AIM security vulnerabilities stem from its legacy architecture, designed during an era when internet threats were less sophisticated than today’s threat landscape. The protocol lacks several modern security features that contemporary communication platforms implement by default. Man-in-the-middle (MITM) attacks represent one of the primary concerns, as AIM’s original design allowed attackers to intercept unencrypted messages between users and servers.
The authentication mechanism in AIM relied on basic username and password combinations without multi-factor authentication (MFA) support. This single-factor authentication approach creates significant risk exposure, particularly in enterprise environments where credential compromise could lead to widespread unauthorized access. Additionally, AIM’s session management protocols contained weaknesses that sophisticated attackers could exploit to hijack active sessions and impersonate legitimate users.
Security researchers have documented numerous CISA-reported vulnerabilities affecting AIM infrastructure. The protocol’s lack of end-to-end encryption means that even with transport layer security (TLS) implementation, message content remains visible to system administrators and potentially vulnerable to insider threats. Organizations must understand these inherent limitations when assessing their current security posture and determining appropriate remediation steps.

Authentication and Access Control Assessment
Evaluating your AIM security authentication framework requires systematic verification of multiple components. First, confirm whether your AIM implementation enforces strong password policies requiring minimum 12-character passwords with complexity requirements including uppercase, lowercase, numeric, and special characters. Weak password enforcement directly correlates with successful account compromise incidents.
Implement role-based access control (RBAC) within your AIM environment by verifying that user permissions align with job responsibilities and organizational hierarchy. Administrative accounts should be separated from standard user accounts, with administrative access requiring additional approval workflows and logging mechanisms. Conduct quarterly access reviews to identify and remediate orphaned accounts, terminated employee access, and privilege creep situations where users retain unnecessary elevated permissions.
Multi-factor authentication represents the most critical missing element in legacy AIM implementations. While native AIM lacks MFA support, consider deploying proxy authentication layers that enforce MFA before granting AIM access. Hardware security keys, time-based one-time passwords (TOTP), and push-based authentication methods significantly increase security posture by requiring attackers to compromise multiple authentication factors simultaneously.
Document your authentication audit findings including:
- Current password policy compliance percentage across all user accounts
- Accounts with administrative privileges and justification for elevated access
- MFA implementation status and coverage across user population
- Failed login attempts over past 90 days indicating potential brute force attacks
- Account lockout policies and duration settings
Encryption and Data Protection Verification
Transport layer security (TLS) encryption must be enabled for all AIM communications between clients and servers. Verify your implementation uses TLS 1.2 or higher, as older SSL/TLS versions (SSL 3.0, TLS 1.0, TLS 1.1) contain cryptographic weaknesses that attackers can exploit. Configure your AIM servers to reject connections using deprecated encryption protocols through strict protocol version enforcement.
Conduct cryptographic cipher suite audits to ensure only strong algorithms remain enabled. Disable weak ciphers including those using RC4, DES, MD5, or export-grade encryption. Modern cipher suites should prioritize authenticated encryption with associated data (AEAD) algorithms such as AES-GCM or ChaCha20-Poly1305. Use NIST guidelines as authoritative references for cryptographic algorithm selection and implementation standards.
Message encryption at rest presents additional challenges within AIM environments. Unlike modern messaging platforms offering end-to-end encryption, AIM stores messages on central servers without encryption by default. Implement database-level encryption using AES-256 for stored messages and sensitive user data. Additionally, configure encrypted backups with separate key management to prevent backup data from becoming attack vectors if primary systems are compromised.
Establish encryption key management procedures including:
- Cryptographic key generation using certified random number generators
- Key storage in hardware security modules (HSMs) or key management systems (KMS)
- Key rotation schedules with quarterly or semi-annual frequency
- Key escrow procedures for compliance and forensic investigation requirements
- Secure key destruction protocols preventing key recovery from decommissioned systems
Network Security and Firewall Configuration
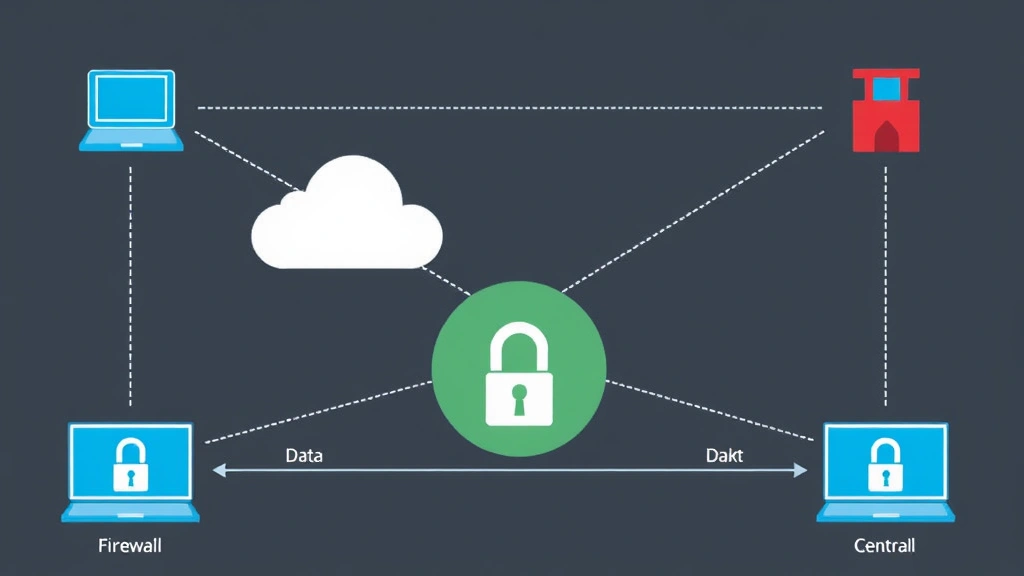
Network segmentation isolates AIM infrastructure from other critical systems, containing potential breaches to minimize organizational impact. Deploy AIM servers within dedicated network segments with restricted access from general user networks. Implement firewall rules explicitly allowing only necessary AIM traffic while blocking all other protocols on AIM server ports.
Verify firewall configurations enforce strict ingress and egress filtering for AIM communications. Legitimate AIM traffic should originate from authorized client networks and administrative management stations only. Block all inbound connections from untrusted internet sources, and implement geo-blocking if your organization operates within specific geographic regions. These network controls prevent unauthorized remote access attempts from compromised external networks.
Configure intrusion detection systems (IDS) and intrusion prevention systems (IPS) to monitor AIM traffic patterns for anomalous behavior. Establish baseline traffic profiles during normal operations, then alert security teams when traffic deviates significantly from established patterns. Detection signatures should identify known attack patterns including credential stuffing attempts, session hijacking indicators, and unusual data exfiltration volumes.
Implement distributed denial-of-service (DDoS) protection mechanisms to maintain AIM availability during coordinated attacks. Rate limiting on AIM server ports prevents attackers from overwhelming services with connection requests. Consider deploying DDoS mitigation services that absorb attack traffic upstream before reaching your infrastructure.
Monitoring and Incident Response
Comprehensive logging captures security-relevant events within your AIM environment for forensic analysis and compliance requirements. Enable detailed audit logging capturing successful and failed authentication attempts, administrative actions, permission changes, and data access events. Centralize logs to security information and event management (SIEM) systems that correlate events across infrastructure components and alert security teams to suspicious patterns.
Configure SIEM rules to detect common AIM attack scenarios including:
- Multiple failed login attempts from single source IP addresses (brute force attacks)
- Successful logins from unusual geographic locations or times
- Administrative account usage during non-business hours
- Bulk message retrieval indicating potential data exfiltration
- Permission elevation requests or privilege escalation attempts
Establish incident response procedures specifically addressing AIM security incidents. Document response workflows including detection, containment, eradication, recovery, and post-incident analysis phases. Designate incident response team members with clear roles and responsibilities. Conduct tabletop exercises quarterly to validate procedures and ensure team familiarity with response protocols.
Implement automated response capabilities that immediately suspend compromised accounts, revoke active sessions, and alert security teams without requiring manual intervention. Faster response times significantly reduce dwell time (duration attackers maintain access) and limit damage from successful compromises.
Migration and Modernization Strategies
Given AIM’s legacy status and inherent security limitations, developing a migration strategy toward modern communication platforms represents best practice. Evaluate contemporary alternatives including Microsoft Teams, Slack, Cisco Webex, or other platforms offering end-to-end encryption, modern authentication mechanisms, and robust security features. Compare platform capabilities against your organizational requirements including compliance obligations, integration needs, and user experience expectations.
Implement phased migration approaches minimizing operational disruption while maintaining business continuity. Establish parallel environments running legacy AIM and new platforms simultaneously during transition periods. Gradually migrate user populations in waves, starting with pilot groups to identify integration issues before organization-wide rollout. Provide comprehensive user training ensuring smooth adoption and reducing support ticket volume.
During migration planning, conduct thorough data preservation assessments. Determine which historical messages require retention for compliance purposes, then export and archive data in secure formats before decommissioning AIM infrastructure. Establish retention schedules aligned with regulatory requirements and organizational policies.
Document lessons learned from your AIM security experience to inform security architecture decisions for new platforms. Evaluate how authentication, encryption, access control, and monitoring will be implemented in replacement systems. Ensure new platforms incorporate security by design principles rather than retrofitting security controls after deployment.
FAQ
What is AIM security and why does it matter?
AIM security refers to protective measures safeguarding AOL Instant Messenger communications and infrastructure from unauthorized access, interception, and data compromise. While AIM officially shut down in 2017, legacy implementations still operate within some organizations, requiring security hardening to meet modern standards and protect sensitive communications.
Is AIM still used in enterprise environments?
Some organizations maintain AIM systems for specific applications or legacy integrations. However, security professionals strongly recommend migrating to modern platforms offering contemporary security features. If AIM remains necessary, implement compensating security controls and prioritize migration planning.
How can I verify if my AIM implementation has current security patches?
Contact your AIM implementation vendor or system administrator to confirm patch status. Review system logs for installation timestamps of security updates. Document all patches applied and establish procedures for testing and deploying future security updates promptly after release.
What are the biggest AIM security risks?
Primary risks include weak authentication mechanisms lacking multi-factor authentication, unencrypted message storage, man-in-the-middle attack vulnerability, and lack of end-to-end encryption. Additionally, legacy protocol design makes AIM susceptible to session hijacking and credential compromise attacks.
How do I implement multi-factor authentication for AIM?
Native AIM lacks built-in MFA support. Implement proxy authentication layers or VPN gateways that enforce MFA before allowing AIM access. Alternatively, use directory services like Active Directory with MFA-capable authentication mechanisms that feed into AIM systems.
What should I do with AIM data during migration?
Conduct data classification assessments determining which messages require retention. Export compliant data in secure formats with encryption. Archive retained data according to regulatory requirements and organizational policies. Securely destroy data no longer requiring retention using certified data destruction methods.
How often should I audit AIM security controls?
Conduct comprehensive security audits quarterly at minimum. Perform monthly access reviews and weekly log analysis. Implement continuous monitoring through SIEM systems providing real-time visibility into security events.


