
Act Security Group: How to Safeguard Your Data?
In an era where cyber threats evolve at unprecedented speeds, understanding how to protect your sensitive information has become essential for both individuals and organizations. Act Security Group represents a comprehensive approach to data protection, combining technical safeguards with strategic security practices. Whether you’re managing personal credentials or enterprise-level data assets, the principles of effective security grouping and access control can mean the difference between a secure digital environment and a catastrophic breach.
Data breaches cost organizations millions annually, with the average breach expense reaching $4.45 million in 2023. Act Security Group methodologies help minimize these risks by implementing layered security protocols that restrict unauthorized access and monitor suspicious activities in real-time. This guide explores essential strategies for safeguarding your data through proper security group implementation, access control management, and proactive threat prevention.
Understanding Act Security Groups and Their Role in Data Protection
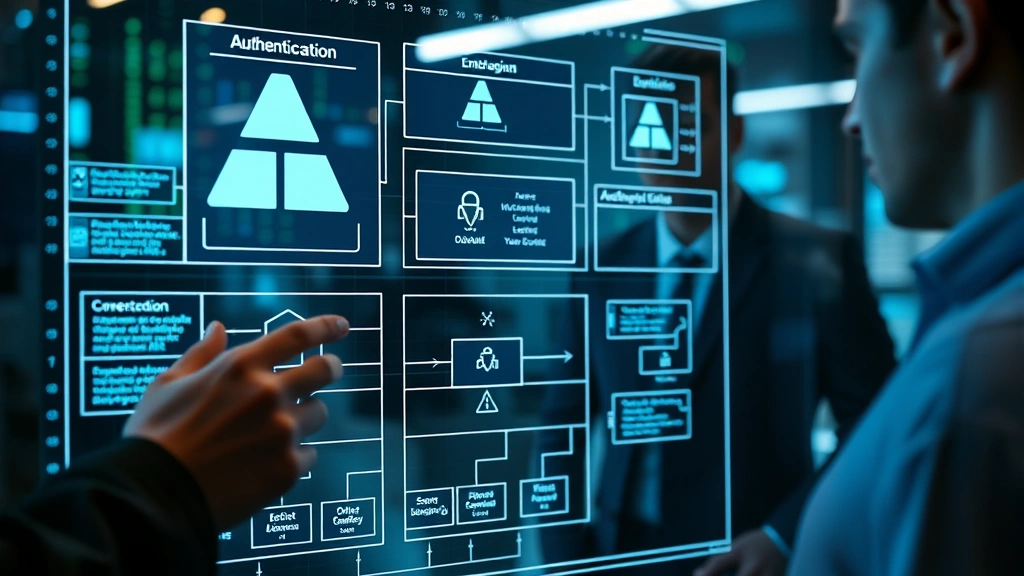
Act Security Groups function as virtual firewalls that control inbound and outbound traffic to your digital assets. These groups define which users, devices, and services can access specific resources within your network infrastructure. Think of them as sophisticated gatekeepers that authenticate identities and verify permissions before granting access to sensitive data.
Security groups operate on a principle of least privilege, meaning users receive only the minimum permissions necessary to perform their job functions. This fundamental concept significantly reduces the attack surface available to potential threats. When properly configured, security groups prevent lateral movement—a technique attackers use to spread through your network after gaining initial access.
The importance of Act Security Groups extends beyond simple access denial. They create an audit trail documenting who accessed what data and when, providing crucial forensic information during security investigations. This accountability mechanism deters insider threats and helps organizations comply with regulatory requirements like HIPAA, GDPR, and SOC 2.
Modern security frameworks recognize that data protection requires multiple overlapping defenses. Security groups form the foundational layer, working in conjunction with encryption, multi-factor authentication, and intrusion detection systems. Organizations implementing comprehensive security strategies across all digital platforms demonstrate stronger overall resilience against cyber attacks.

Implementing Effective Access Control Mechanisms
Access control represents the cornerstone of any robust data protection strategy. Role-Based Access Control (RBAC) assigns permissions based on job functions rather than individual characteristics. For example, finance department members receive access to accounting systems, while marketing personnel access content management platforms. This approach scales efficiently across organizations of any size.
Attribute-Based Access Control (ABAC) provides more granular control by considering multiple factors: user location, device security status, time of day, and data classification level. When an employee attempts accessing sensitive information from an unfamiliar location outside business hours on an unmanaged device, ABAC systems can trigger additional verification steps or deny access entirely.
Implementing effective access control requires several critical steps:
- Inventory all data assets and classify them by sensitivity level—public, internal, confidential, or restricted
- Map user roles to specific data categories and operations they legitimately require
- Establish approval workflows for access requests with appropriate oversight
- Implement time-based access that automatically revokes permissions after project completion
- Create exception handling procedures for emergency access scenarios with enhanced monitoring
- Review permissions quarterly to identify and remove unnecessary access
Organizations should regularly audit their access control policies against industry standards. NIST cybersecurity frameworks provide comprehensive guidelines for implementing controls that balance security with operational efficiency. The principle of separation of duties ensures no single person controls all aspects of critical processes, reducing fraud and error risks.
Network Segmentation and Security Group Configuration
Network segmentation divides your infrastructure into isolated zones, each with its own security policies and monitoring. This architectural approach prevents attackers from accessing your entire network if they breach a single segment. Security groups enforce these boundaries by controlling traffic flow between zones.
Consider a healthcare organization protecting patient data. The network might segment into administrative zones, clinical systems, research databases, and public-facing portals. Security groups ensure that administrative staff cannot directly access research databases, and public-facing systems cannot communicate with clinical networks. If attackers compromise the public portal, segmentation limits their ability to reach sensitive patient information.
Effective network segmentation requires careful planning:
- Identify critical assets requiring highest protection levels
- Group systems by function and security requirements
- Design network topology with clear separation between zones
- Configure security groups to enforce allowed connections only
- Implement monitoring for inter-segment traffic to detect anomalies
- Test security group rules regularly to ensure effectiveness
Zero-trust architecture takes segmentation further by requiring verification for every access request, regardless of origin. Traditional networks trusted internal traffic implicitly; zero-trust assumes all traffic could be malicious. Security groups in zero-trust environments operate with explicit allow-lists rather than deny-lists, creating significantly stronger protection postures.
Cloud environments benefit particularly from robust security group configuration. Virtual machines, databases, and containers can scale rapidly, making manual access control impractical. Security groups automate enforcement across dynamic infrastructure, adapting as resources spin up and down.
Monitoring and Auditing Security Group Activities
Implementing security groups represents only the first step; continuous monitoring ensures they function as intended. Log aggregation systems collect access attempts, configuration changes, and policy violations from across your infrastructure. Security analysts review these logs to identify suspicious patterns requiring investigation.
Real-time alerting systems should trigger notifications for critical events:
- Multiple failed authentication attempts from the same source
- Access to sensitive data outside normal business hours
- Unusual geographic locations accessing restricted resources
- Unauthorized modifications to security group rules
- Mass data downloads or exports
- Privilege escalation attempts
Security Information and Event Management (SIEM) platforms correlate events from multiple sources to detect sophisticated attacks that individual logs might miss. A single failed login attempt appears harmless, but SIEM systems can identify patterns—the same attacker trying thousands of credentials across different accounts simultaneously.
Regular access reviews ensure permissions remain appropriate as employees change roles or leave organizations. Stale access—permissions granted months ago for temporary projects—creates unnecessary risk. Automated workflows can prompt managers to review their team’s access quarterly, with non-responses triggering escalation to security teams.
Audit reports documenting security group configurations, access approvals, and monitoring results satisfy regulatory requirements and provide evidence of due diligence. These reports prove organizations took reasonable steps to protect data, crucial during breach investigations or compliance audits.
Best Practices for Data Protection Compliance
Regulatory frameworks increasingly mandate specific data protection controls. CISA provides authoritative guidance on implementing federal cybersecurity standards. Organizations handling regulated data must understand applicable requirements and implement corresponding controls.
GDPR requires organizations to implement technical and organizational measures protecting personal data. Security groups support this requirement by restricting access to personal information. When individuals request data deletion under GDPR’s right to be forgotten, security groups can prevent any access to retained records pending purge.
HIPAA compliance for healthcare organizations demands access controls restricting health information to authorized personnel. Security groups enforce this requirement by segregating clinical systems. Audit logs prove that unauthorized individuals never accessed protected health information, essential during compliance investigations.
PCI-DSS standards for payment card data require restricting access to card numbers and security codes. Security groups limit which systems can store or process cardholder information, isolating payment systems from general-purpose networks. This segmentation prevents attackers from stealing card data even if they compromise other parts of your network.
SOC 2 Type II compliance requires demonstrating consistent control operation over extended periods. Security group configurations, access reviews, and monitoring logs provide evidence of control effectiveness. Regular testing proves controls function as designed, not just theoretically.
Data protection compliance extends beyond regulatory requirements to include contractual obligations. Business associates processing data on behalf of primary organizations must implement equivalent security controls. Security group configurations should enforce these requirements automatically, preventing data exposure regardless of human oversight lapses.
Common Vulnerabilities and How to Address Them
Even well-intentioned security group implementations contain vulnerabilities. Overly permissive rules grant excessive access, defeating the purpose of segmentation. Rules allowing access from “0.0.0.0/0” (any source) on critical ports should trigger immediate remediation.
Configuration drift occurs when security group rules change without documentation or approval. Over time, temporary exceptions become permanent, and emergency access rules remain active long after their purpose expires. Version control systems and infrastructure-as-code practices prevent drift by ensuring all changes receive approval and remain documented.
Shadow IT—unauthorized systems operating outside official security frameworks—bypasses security group protections entirely. Employees might install unapproved cloud services to simplify workflows, creating data exposure risks. Organizations should establish approved tools and make compliant options convenient to reduce unauthorized workarounds.
Insider threats represent a significant vulnerability that security groups alone cannot prevent. Employees with legitimate access might exfiltrate data for personal gain or competitive advantage. Monitoring unusual access patterns—particularly from privileged accounts—helps detect insider threats before significant damage occurs.
Credential compromise affects security group effectiveness if attackers obtain valid credentials. Even if security groups restrict access to administrative accounts, compromised credentials allow attackers to authenticate as authorized users. Multi-factor authentication significantly increases credential compromise difficulty, requiring attackers to bypass additional verification layers.
Default configurations in cloud platforms often create unintended security group vulnerabilities. Databases might be publicly accessible by default, exposing data to internet-scale attacks. Automated scanning tools should regularly verify security group configurations match organizational standards, alerting teams to deviations.
API access control requires special attention in modern architectures. Microservices communicate through APIs that must authenticate and authorize requests. Security groups protecting API endpoints should enforce strong authentication and validate all requests, preventing unauthorized service-to-service communication.
Mobile and remote access introduces complexity to security group enforcement. Users accessing corporate resources from personal devices on home networks require different controls than office-based systems. Zero-trust network access solutions provide consistent protection regardless of location or device.
FAQ
What is an Act Security Group and how does it differ from traditional firewalls?
Act Security Groups operate at application and network levels, controlling access to specific resources based on identity and context. Traditional firewalls filter traffic based on IP addresses and ports. Security groups combine firewall functionality with identity verification and attribute-based access control, providing more granular protection. Where firewalls ask “is this traffic allowed?”, security groups ask “is this authenticated user authorized to access this specific resource?”
How frequently should security group configurations be reviewed?
Security group configurations should undergo formal review quarterly at minimum, with informal reviews during access changes. Rules added for temporary purposes require documented expiration dates with automatic removal. Critical systems warrant monthly reviews, and any suspected compromise should trigger immediate audit of relevant security groups.
Can security groups prevent all data breaches?
Security groups form one component of comprehensive data protection strategies but cannot prevent breaches independently. They must work alongside encryption, authentication, monitoring, incident response, and employee training. Organizations implementing security groups as their only protection remain vulnerable to insider threats, social engineering, and zero-day exploits.
What tools help manage Act Security Groups at scale?
Infrastructure-as-code tools like Terraform and CloudFormation define security group rules programmatically, enabling version control and consistent deployment. Cloud-native platforms provide built-in security group management dashboards. Third-party tools like Cloudflare and similar providers offer advanced security group management with threat intelligence integration.
How do security groups integrate with zero-trust architecture?
Zero-trust architecture requires continuous verification for every access request. Security groups enforce this principle by using explicit allow-lists rather than deny-lists, requiring positive authentication rather than assuming trust. Device posture checking ensures only compliant systems access resources, and continuous monitoring detects compromise indicators.
What compliance frameworks specifically require security group implementation?
NIST Cybersecurity Framework, HIPAA, GDPR, PCI-DSS, and SOC 2 all require access controls that security groups help implement. However, these frameworks mandate the security outcome (restricting unauthorized access) rather than specific technical implementation. Security groups represent one effective method of achieving compliance, but alternatives exist depending on organizational context.
How can organizations test security group effectiveness?
Penetration testing simulates attacker behavior to identify security group misconfigurations. Red team exercises attempt unauthorized access, validating that security groups prevent compromise. Regular access reviews confirm permissions align with job functions. Logging analysis verifies that denied access attempts appear in audit trails, confirming security groups function properly.


