
Is Your Home Network Secure? Expert Analysis Inside
Your home network is the digital backbone of modern living, connecting everything from smartphones and laptops to smart home devices and security cameras. Yet most homeowners treat their Wi-Fi routers like invisible utilities, rarely thinking about the security implications until something goes wrong. The truth is alarming: inadequately secured home networks serve as entry points for cybercriminals, hackers, and malware that can compromise personal data, financial information, and device integrity.
In an era where remote work, online banking, and smart home automation have become standard, understanding home network security isn’t optional—it’s essential. This comprehensive guide examines the vulnerabilities lurking in typical home networks and provides actionable strategies to fortify your digital perimeter. Whether you’re streaming content from the best movies on Netflix or managing sensitive financial documents, your network deserves professional-grade protection.
Cyber threats targeting home networks have become increasingly sophisticated. From credential harvesting to man-in-the-middle attacks, the risks are real and growing. This analysis draws on security industry best practices and expert recommendations to help you assess and improve your home network’s security posture.
Understanding Home Network Vulnerabilities
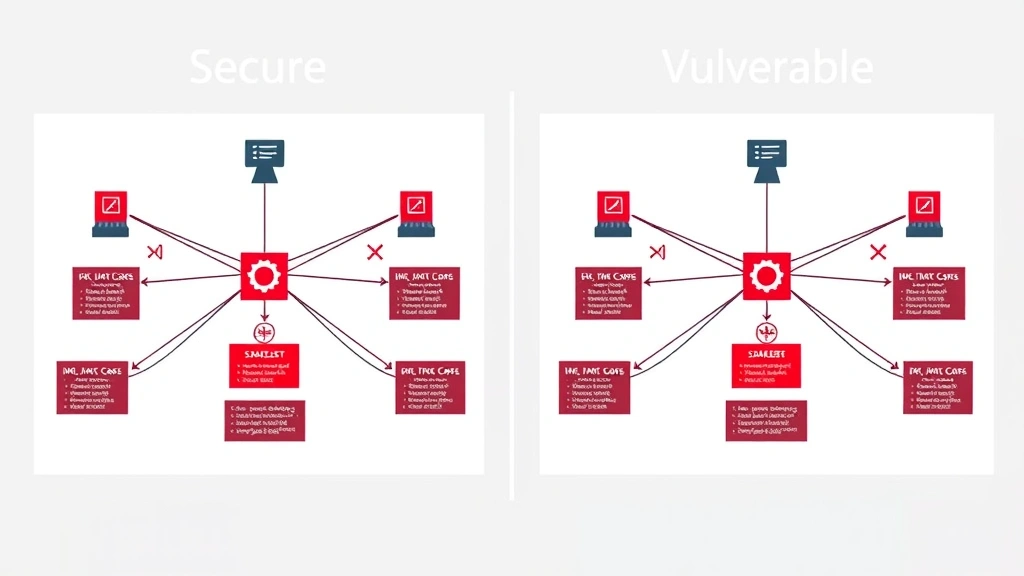
Home networks typically consist of a router, modem, and numerous connected devices—smartphones, tablets, computers, smart TVs, thermostats, and security systems. Each device represents a potential vulnerability. Unlike enterprise networks with dedicated IT teams and security infrastructure, home networks often lack basic protective measures.
The most common vulnerabilities include weak passwords, outdated firmware, unencrypted connections, and insufficient network segmentation. The Cybersecurity and Infrastructure Security Agency (CISA) regularly warns about the dangers of neglected home network security. Attackers exploit these weaknesses to gain unauthorized access, intercept traffic, or launch attacks against other systems.
Many homeowners don’t realize their network is compromised until significant damage occurs. By then, personal data may have been stolen, financial accounts drained, or devices infected with malware. The National Institute of Standards and Technology (NIST) emphasizes that proactive security measures are far more cost-effective than remediation after an incident.
Understanding your network’s attack surface is the first step toward securing it. This includes identifying all connected devices, understanding data flows, and recognizing where attackers might intercept communications or exploit weaknesses.

Default Settings: Your First Security Mistake
One of the most critical security failures in home networks stems from leaving router default settings unchanged. Manufacturers ship routers with generic admin credentials, default Wi-Fi names (SSIDs), and weak or no encryption enabled. This is done for convenience, not security.
When you set up a router, the first action should be changing the default administrator username and password. Use a strong, unique password—at least 16 characters combining uppercase, lowercase, numbers, and special characters. Many people use simple passwords like “admin123” or “password,” which take seconds to crack.
The default SSID (network name) often reveals your router model and manufacturer. Attackers use this information to target known vulnerabilities in that specific model. Change your SSID to something generic that doesn’t identify your hardware or personal information. Avoid names like “[YourName]’s WiFi” or “[AddressNumber] Network.”
Disable WPS (Wi-Fi Protected Setup) completely. This feature was designed for convenience but creates a significant security hole. WPS allows devices to connect with an eight-digit PIN, and attackers can brute-force this PIN in hours. Most modern routers allow disabling WPS through the admin interface.
Enable UPnP (Universal Plug and Play) only if absolutely necessary. While convenient for device discovery, UPnP can allow malware to open ports and create backdoors on your router. If you don’t actively use features requiring UPnP, disable it.
Wi-Fi Encryption and Authentication Methods
Wireless encryption is your network’s primary defense against unauthorized access and eavesdropping. The encryption standard you use dramatically impacts security. Never use WEP (Wired Equivalent Privacy) or WPA (Wi-Fi Protected Access)—both are cryptographically broken and can be cracked in minutes.
WPA2 (Wi-Fi Protected Access II) was the gold standard for over a decade. It uses AES encryption and provides reasonable security for home networks. However, WPA3, released in 2018, represents a significant security upgrade. WPA3 includes stronger encryption, protection against brute-force password attacks, and enhanced security for IoT devices.
If your router supports WPA3, enable it immediately. If not, WPA2 is acceptable, but you should consider upgrading your router. Many routers from 2015 or earlier don’t support WPA3. Check your router’s specifications or contact the manufacturer to confirm.
The password you set for your Wi-Fi network is critical. Use a passphrase of at least 20 characters—the longer the better. Include a mix of character types and avoid dictionary words, personal information, or common patterns. A strong Wi-Fi password is your first line of defense against unauthorized network access.
Consider using a VPN (Virtual Private Network) for all network traffic. A quality VPN encrypts all data traveling between your devices and the VPN provider’s server, protecting against eavesdropping even on compromised networks. This is particularly important if you handle sensitive information like banking or medical data.
Device Management and Network Segmentation
Modern homes often contain 20-50 connected devices. Managing security across this many devices is challenging but essential. Start by creating an inventory of all connected devices, including their IP addresses, default passwords, and firmware versions.
Network segmentation involves dividing your network into separate zones with different security levels. Your primary network might contain trusted devices like your primary computer and smartphone. A separate IoT network could isolate smart home devices, which often have weaker security and receive infrequent updates.
Most modern routers support creating guest networks—use this feature to isolate devices you don’t fully trust or that connect infrequently. Guest networks should have different credentials and be configured with the same encryption standards as your main network.
Regularly update firmware on all network devices. Firmware updates patch security vulnerabilities that attackers actively exploit. Check your router manufacturer’s website monthly for updates. Many modern routers support automatic updates—enable this if available.
Change default passwords on all connected devices, particularly security cameras, smart speakers, and network-attached storage. Many IoT devices ship with well-known default credentials that attackers test immediately upon gaining network access.
Remove or disable unnecessary services on your router. Many routers include features like remote management, UPnP, and file sharing that most users never use. Each enabled service represents a potential attack vector. Disable everything you don’t actively use.
Advanced Security Measures for Home Networks
Beyond basic security, advanced measures provide additional protection. A network firewall—either built into your router or a separate device—filters incoming and outgoing traffic based on rules you define. Most routers include basic firewall functionality; ensure it’s enabled.
MAC address filtering allows you to specify which devices can connect to your network based on their hardware addresses. This prevents unauthorized devices from connecting even if they know your Wi-Fi password. However, MAC addresses can be spoofed, so this shouldn’t be your only security measure.
Disabling SSID broadcast (making your network “hidden”) provides minimal security—the SSID is still transmitted in probe requests—but it does prevent casual scanning. Combined with other security measures, hiding your SSID adds a small layer of obscurity.
DNS filtering protects against malicious websites and phishing attacks by blocking requests to known dangerous domains. Services like Cloudflare’s 1.1.1.1 for Families or Quad9 provide free DNS filtering at the network level. Configure your router to use these services instead of your ISP’s DNS servers.
Consider implementing a network-level ad blocker and malware filter. Services like Pi-hole create a DNS-level filter that blocks advertisements and malicious domains across all connected devices. This reduces bandwidth consumption and protects against malware distribution networks.
Enable logging on your router to track connection attempts and network activity. While most users won’t regularly review logs, they become invaluable if you suspect a security incident. Store logs securely or export them regularly to separate storage.
Monitoring and Threat Detection
Passive security measures only go so far. Active monitoring helps detect when something goes wrong. Regularly review the list of connected devices on your router’s admin interface. Unknown devices should be investigated and removed immediately.
Monitor your network’s bandwidth usage for anomalies. A sudden spike in outbound traffic might indicate malware on a device sending data to attackers. Most routers provide basic bandwidth monitoring; more detailed analysis requires separate tools.
Check router logs for suspicious login attempts or unusual activity. Failed authentication attempts from foreign IP addresses suggest someone is trying to breach your admin interface. If you see repeated attempts, change your admin password immediately.
Use network scanning tools like Nmap or Zenmap to identify open ports and services on your network. Unnecessary open ports represent attack vectors. Close any ports you don’t actively use through your router’s firewall configuration.
Consider implementing a security information and event management (SIEM) solution designed for home networks. While traditional SIEM systems are enterprise-focused, home-friendly alternatives now exist. These tools aggregate logs from various network devices and alert you to suspicious patterns.
Maintain regular backups of critical data. If a ransomware attack or data breach occurs, backups allow you to recover without paying attackers or losing irreplaceable information. Store backups offline or in a secure cloud service separate from your primary network.
Creating a Security Maintenance Schedule
Home network security isn’t a one-time configuration—it requires ongoing maintenance. Establish a regular schedule to check security settings, update firmware, and review access logs.
Monthly tasks should include checking for router firmware updates, reviewing connected devices for unfamiliar entries, and verifying firewall settings remain enabled. Set calendar reminders to ensure consistency.
Quarterly, conduct a more thorough review. Change your Wi-Fi password (or at minimum, rotate admin credentials). Review and update device inventory, checking for firmware updates on connected devices. Test your network’s security using online tools.
Annually, perform a comprehensive security assessment. This might include hiring a professional penetration tester to identify vulnerabilities, updating your router if it no longer receives security patches, or reconfiguring network segmentation based on new devices.
Document all security configurations, passwords, and device information in a secure location. Encrypted password managers like Bitwarden or 1Password work well for this purpose. This documentation proves invaluable when troubleshooting issues or onboarding new devices.
Stay informed about emerging threats. Follow security researchers and organizations like Bleeping Computer for news about vulnerabilities affecting home network equipment. Subscribe to manufacturer security bulletins for your specific router model.
For additional guidance, consult the NIST Cybersecurity Framework, which provides comprehensive guidelines applicable to home networks. While designed for organizations, many principles scale down effectively for residential use.
Remember that perfect security doesn’t exist, but reasonable security measures significantly reduce your risk. By implementing these strategies, you transform your home network from a vulnerability into a properly defended digital asset.
FAQ
How often should I change my Wi-Fi password?
Change your Wi-Fi password at least quarterly, or immediately if you suspect unauthorized access. If someone moves out of your home, change it promptly. Unlike some security practices, frequent password changes provide real benefits for Wi-Fi security since network access is difficult to monitor continuously.
Should I hide my Wi-Fi network?
Hiding your SSID provides minimal security benefit since the network name is transmitted in probe requests. However, it does prevent casual discovery and can be part of a layered security approach. Don’t rely on SSID hiding alone; combine it with strong encryption and authentication.
Is WPA2 still secure enough?
WPA2 remains reasonably secure for home networks, though WPA3 is preferable. If your router doesn’t support WPA3, WPA2 is acceptable, but you should plan to upgrade your router within the next 2-3 years as WPA3-capable routers become standard.
Do I need a separate firewall for home networks?
Most modern routers include adequate firewall functionality for home use. A separate firewall device provides additional protection but increases complexity and cost. Unless you have specific advanced requirements, your router’s built-in firewall is sufficient when properly configured.
How can I tell if my network has been compromised?
Signs of compromise include unexplained bandwidth usage, slow device performance, unfamiliar devices in your network, frequent disconnections, or suspicious login attempts in router logs. If you suspect compromise, change all passwords, update firmware, and consider resetting your router to factory settings and reconfiguring from scratch.
What’s the difference between network security and device security?
Network security protects the infrastructure and communication channels (router, Wi-Fi, connections between devices). Device security protects individual computers, phones, and IoT devices (antivirus, updates, passwords). Both are essential; compromised network security can expose even well-secured devices, and vice versa.


