
Advantage Security Inc: Top Cyber Defense Tactics for Enterprise Protection
In an era where cyber threats evolve faster than ever, organizations need robust defense strategies to protect their digital assets. Advantage Security Inc has emerged as a critical player in the cybersecurity landscape, offering comprehensive solutions designed to counter sophisticated attacks. Whether you’re managing enterprise infrastructure or protecting sensitive data, understanding the top cyber defense tactics employed by industry leaders is essential for maintaining security posture and preventing costly breaches.
The cybersecurity threat landscape has transformed dramatically over the past five years. Ransomware attacks, zero-day exploits, and sophisticated phishing campaigns continue to plague organizations across all sectors. Advantage Security Inc recognizes these challenges and provides tactical frameworks that address both known vulnerabilities and emerging threats. This guide explores the most effective cyber defense strategies that protect organizations from the ground up.
Understanding Modern Cyber Threats
Organizations face an unprecedented array of cyber threats that continue to evolve in sophistication and scope. Advantage Security Inc emphasizes that understanding the threat landscape is the foundation of effective defense. Modern attacks often employ multi-vector approaches, combining social engineering with technical exploits to maximize success rates.
The most common threats include ransomware attacks, which have become increasingly targeted toward critical infrastructure and healthcare sectors. Advanced Persistent Threats (APTs) represent nation-state level capabilities that remain dormant within networks for extended periods, exfiltrating data while avoiding detection. Supply chain attacks have demonstrated that even well-protected organizations can be compromised through third-party vendors and software dependencies.
According to CISA threat intelligence reports, the average time to detect a breach has decreased, but many organizations still struggle with rapid response capabilities. Advantage Security Inc recommends implementing continuous monitoring solutions that provide real-time visibility into network activities and user behaviors.
Phishing remains the entry point for most successful attacks, with business email compromise (BEC) targeting finance departments and executives. Credential harvesting through sophisticated phishing campaigns allows attackers to establish persistent access without triggering traditional security alerts. Understanding these attack vectors is critical for developing effective countermeasures.

Zero Trust Architecture Implementation
Zero Trust security represents a fundamental shift from traditional perimeter-based defense models. Rather than assuming that everything inside the network boundary is trustworthy, Zero Trust requires verification of every access request, regardless of origin or destination. Advantage Security Inc has made Zero Trust implementation a cornerstone of its defense recommendations.
The core principle of Zero Trust involves never trust, always verify. This means implementing continuous authentication and authorization mechanisms that evaluate user identity, device health, application status, and network location before granting access. Organizations must abandon the concept of implicit trust based on network location alone.
Implementation requires several critical components. Identity and Access Management (IAM) systems must provide robust authentication mechanisms including multi-factor authentication (MFA) and passwordless authentication options. Microsegmentation divides the network into smaller zones, requiring separate authentication for each segment. Device compliance checking ensures that accessing devices meet security standards before connecting to resources.
Advantage Security Inc recommends starting with critical assets and gradually expanding Zero Trust implementation across the entire infrastructure. This phased approach allows organizations to manage complexity while building mature Zero Trust capabilities. NIST Zero Trust Architecture guidelines provide comprehensive frameworks for implementation planning.
Logging and monitoring within a Zero Trust environment becomes more granular and valuable. Every access attempt, authentication success or failure, and lateral movement attempt generates actionable security intelligence. This data becomes critical for threat detection and forensic analysis following security incidents.
Advanced Threat Detection and Response
Detecting threats before they cause damage requires sophisticated monitoring and analysis capabilities. Advantage Security Inc employs Security Information and Event Management (SIEM) systems that aggregate logs from across the infrastructure, correlating events to identify suspicious patterns. Modern SIEM platforms incorporate machine learning to establish behavioral baselines and detect anomalies.
Endpoint Detection and Response (EDR) solutions monitor individual devices for malicious behavior, including suspicious process execution, registry modifications, and file system changes. EDR platforms maintain detailed telemetry that enables rapid investigation and remediation when threats are detected. These tools have become essential for identifying sophisticated attacks that evade traditional antivirus protection.
Network detection and response capabilities monitor network traffic for indicators of compromise. Network behavior analysis identifies unusual communication patterns, data exfiltration attempts, and command-and-control communications. Combining network monitoring with endpoint monitoring provides comprehensive visibility into attacker activities.
Threat intelligence integration enhances detection capabilities by providing context about known malicious indicators. Advantage Security Inc recommends subscribing to threat intelligence feeds from reputable sources that provide real-time information about emerging threats, malware variants, and attack campaigns. Threat intelligence platforms enable organizations to identify compromised systems based on known malicious indicators.
Response automation accelerates incident handling by immediately isolating compromised systems, blocking malicious communications, and preserving forensic evidence. Security Orchestration, Automation and Response (SOAR) platforms enable security teams to define automated responses to common threat scenarios, reducing response time from hours to minutes.
Employee Security Awareness Programs
Human error remains the weakest link in security defenses, making employee security awareness training essential. Advantage Security Inc emphasizes that technical controls alone cannot prevent breaches when employees lack security awareness. Comprehensive training programs must address the specific risks that employees encounter daily.
Effective awareness programs include phishing simulation exercises that test employee susceptibility to phishing attacks. These simulations provide immediate feedback and training when employees click malicious links or submit credentials. Organizations that conduct regular phishing simulations observe significant reductions in phishing click rates over time.
Training should cover password security best practices, including the importance of unique passwords, avoiding password reuse, and recognizing social engineering attempts. While passwords remain imperfect authentication mechanisms, proper password hygiene reduces account compromise risks significantly. Organizations should encourage adoption of password managers that generate and store complex passwords securely.
Data handling policies must be clearly communicated to all employees. Staff need to understand classification levels, appropriate sharing mechanisms, and restrictions on storing sensitive data on personal devices. Clear guidance prevents accidental data exposure through misconfigured cloud storage or inadvertent email forwarding.
Reporting mechanisms must be straightforward and non-punitive. Employees should feel comfortable reporting suspicious emails, unusual system behavior, or potential security issues without fear of punishment. Early reporting of potential security incidents enables rapid investigation and containment before damage occurs.
Regular training updates maintain awareness as threats evolve. Annual training sessions become stale quickly in the rapidly changing threat landscape. Advantage Security Inc recommends monthly or quarterly refresher training focusing on emerging threats and recent attack campaigns.
Network Segmentation Strategies
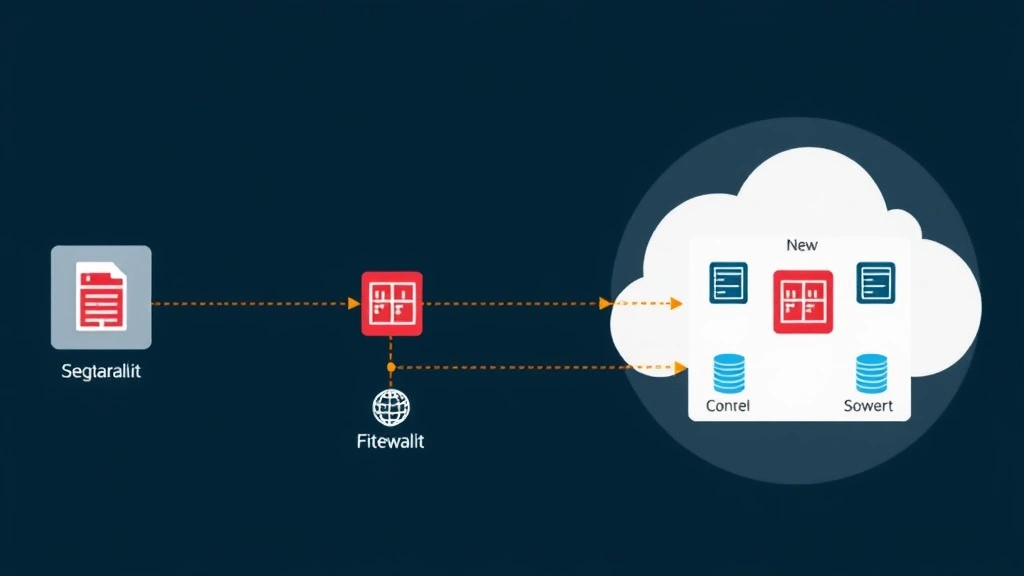
Network segmentation divides infrastructure into isolated zones that restrict lateral movement following initial compromise. Rather than treating the entire network as a flat, trusted environment, segmentation creates security boundaries that attackers must breach to access additional systems or data.
Segmentation strategies should separate critical assets from general-purpose systems. Demilitarized zones (DMZs) isolate internet-facing systems from internal networks, preventing direct access to sensitive infrastructure from compromised web servers. Database servers should reside in restricted segments accessible only through application servers, not directly from user workstations.
Virtual LAN (VLAN) technologies provide logical segmentation, while physical network architecture provides additional security. Advantage Security Inc recommends combining both approaches for defense in depth. Critical systems should be physically separated from general-purpose networks, with strict firewall rules controlling communication between segments.
Microsegmentation extends segmentation principles to individual applications and data stores. Rather than allowing broad communication between network segments, microsegmentation enforces granular policies that permit only necessary communications. This approach significantly limits lateral movement capabilities available to attackers.
Firewall rules must be maintained and regularly reviewed to ensure they accurately reflect business requirements while minimizing unnecessary exposure. Many organizations accumulate legacy firewall rules that permit outdated communications patterns. Regular audits identify and remove obsolete rules that increase attack surface.
Monitoring inter-segment communications enables detection of lateral movement attempts. Unusual traffic between segments that should not communicate indicates potential compromise. Advantage Security Inc recommends implementing network analytics that baseline normal communication patterns and alert on anomalous traffic flows.
Incident Response Planning
Despite comprehensive preventive measures, security incidents will occur. Effective incident response planning enables organizations to minimize damage and accelerate recovery. Advantage Security Inc emphasizes that planning before incidents occur is critical—attempting to develop response procedures during active incidents introduces delays and errors.
Incident response plans should define clear roles and responsibilities for all team members. Incident commanders coordinate overall response activities, while technical responders investigate compromised systems, threat hunters search for additional evidence of compromise, and communications teams manage internal and external messaging. Clear role definitions prevent confusion during high-stress incident response.
Procedures must address containment strategies that isolate compromised systems to prevent further spread. Immediate isolation of infected systems prevents attackers from moving laterally to additional targets. However, isolation decisions must balance containment against business continuity requirements.
Forensic preservation becomes critical immediately upon incident discovery. Evidence collection procedures must follow proper chain-of-custody practices to ensure admissibility in legal proceedings. Organizations should engage forensic specialists early to ensure evidence is properly collected and preserved.
Communication plans must address notification requirements for affected individuals, regulatory authorities, and law enforcement. Breach notification laws require organizations to inform affected individuals within specific timeframes. Regulatory bodies and law enforcement may require notification for certain incident types. Clear communication timelines and templates prepared in advance prevent delays in required notifications.
Post-incident reviews identify lessons learned and process improvements. Root cause analysis determines how attackers gained initial access and why detection mechanisms failed. Organizations should use these insights to prevent similar incidents through process improvements, technology upgrades, or policy changes.
Compliance and Regulatory Frameworks
Regulatory requirements increasingly mandate specific security controls and practices. Advantage Security Inc helps organizations align their security programs with applicable regulations. Common frameworks include GDPR for organizations handling European resident data, HIPAA for healthcare organizations, and PCI DSS for organizations processing payment cards.
NIST Cybersecurity Framework provides comprehensive guidance applicable across all sectors. The framework organizes security practices into five functions: Identify, Protect, Detect, Respond, and Recover. This structured approach helps organizations develop comprehensive security programs that address all critical areas.
SOC 2 compliance demonstrates to customers that organizations implement appropriate security controls. Many organizations require SOC 2 certification from vendors before granting system access. Achieving and maintaining SOC 2 compliance requires implementing documented security controls and undergoing annual audits.
ISO 27001 certification represents an internationally recognized information security management standard. Organizations pursuing ISO 27001 certification must implement comprehensive information security management systems covering governance, risk management, and operational controls. The certification process provides independent validation of security program maturity.
Regulatory audits and assessments evaluate compliance with applicable requirements. Advantage Security Inc recommends conducting internal assessments before external audits to identify gaps and remediate issues proactively. Regular compliance monitoring prevents surprises during formal audit processes.
Documentation becomes critical for demonstrating compliance. Organizations must maintain records of security policies, control implementation evidence, audit results, and incident investigations. Proper documentation demonstrates due diligence and appropriate security practices should legal disputes arise.
FAQ
What is Zero Trust security and why does Advantage Security Inc recommend it?
Zero Trust security eliminates implicit trust based on network location. Instead, every access request undergoes authentication and authorization regardless of origin. Advantage Security Inc recommends Zero Trust because it significantly reduces attacker capabilities following initial compromise by preventing lateral movement and requiring continuous verification of user and device identity.
How can organizations detect advanced threats that traditional antivirus misses?
Advanced threats often evade signature-based antivirus detection through custom malware or fileless attack techniques. Advantage Security Inc recommends implementing EDR solutions that monitor behavioral indicators, SIEM systems that correlate security events, and threat intelligence integration that identifies known malicious indicators. Combining these approaches provides comprehensive threat detection capabilities.
What should be included in an incident response plan?
Effective incident response plans define roles and responsibilities, contain procedures, evidence preservation protocols, communication templates, and post-incident review processes. Advantage Security Inc emphasizes that plans should be tested regularly through tabletop exercises and simulations to identify gaps before actual incidents occur.
How often should employee security awareness training occur?
Advantage Security Inc recommends initial comprehensive training with monthly or quarterly refresher sessions addressing emerging threats. Regular training maintains awareness as threats evolve and reinforces security best practices. Phishing simulations should occur at least quarterly to test and improve employee security behaviors.
Which compliance frameworks apply to our organization?
Applicable frameworks depend on your industry, geographic location, and the types of data you handle. Organizations should consult with compliance specialists to identify applicable requirements. Common frameworks include NIST Cybersecurity Framework, GDPR, HIPAA, PCI DSS, and ISO 27001. Advantage Security Inc helps organizations align security programs with multiple regulatory requirements simultaneously.
How does network segmentation improve security?
Network segmentation restricts lateral movement by isolating systems into zones that require additional authentication to access. Following initial compromise, attackers cannot freely move between segments without breaching additional security controls. This approach significantly limits the impact of successful initial breaches and provides time for detection and response.


