
Boost Cybersecurity: Expert ACT Security Insights
In today’s digital landscape, cybersecurity has become non-negotiable for organizations of all sizes. ACT Security represents a comprehensive framework designed to address the evolving threat landscape while maintaining operational efficiency. Whether you’re managing enterprise infrastructure or protecting sensitive data, understanding ACT Security principles can significantly strengthen your defensive posture against sophisticated cyber threats.
The modern threat environment demands more than traditional perimeter defenses. ACT Security integrates assessment, containment, and threat management into a cohesive strategy that enables organizations to detect, respond to, and recover from security incidents with greater speed and precision. This expert guide explores the fundamental concepts, implementation strategies, and best practices that can transform your organization’s security capabilities.
Understanding ACT Security Framework
ACT Security operates on three pillars: Assessment, Containment, and Threat management. This framework provides organizations with a structured approach to identifying vulnerabilities, isolating threats, and implementing comprehensive countermeasures. Unlike reactive security models that respond only after breaches occur, ACT Security emphasizes proactive identification and mitigation of potential risks before they materialize into significant incidents.
The Assessment component involves continuous evaluation of your organization’s security infrastructure, applications, and processes. This includes vulnerability scanning, penetration testing, and security audits that reveal weaknesses before attackers exploit them. Containment focuses on isolating affected systems and limiting the spread of threats throughout your network. Threat management encompasses intelligence gathering, analysis, and strategic response planning that enables your team to stay ahead of emerging attack vectors.
Organizations implementing ACT Security frameworks often reference guidelines from CISA (Cybersecurity and Infrastructure Security Agency), which provides authoritative standards for federal and critical infrastructure protection. These frameworks align with NIST cybersecurity guidelines that establish best practices for risk management across all sectors.
Assessment Phase: Evaluating Your Security Posture
The assessment phase forms the foundation of effective ACT Security implementation. This stage requires comprehensive evaluation of your current security infrastructure, identifying gaps, weaknesses, and areas requiring immediate attention. A thorough assessment provides the baseline data necessary for strategic planning and resource allocation.
Vulnerability Assessment and Scanning
Automated vulnerability scanning tools identify known security flaws in your systems, applications, and network infrastructure. These tools compare your environment against established vulnerability databases and security benchmarks, generating detailed reports of findings organized by severity level. Regular scanning—ideally continuous in modern environments—ensures you maintain awareness of emerging vulnerabilities as new threats are discovered.
Penetration Testing and Red Team Exercises
Beyond automated scanning, penetration testing simulates real-world attacks conducted by skilled professionals who attempt to breach your defenses. These exercises reveal how attackers might chain multiple vulnerabilities together or exploit human factors to gain access. Red team exercises extend this concept further, testing your organization’s detection and response capabilities against sophisticated, persistent threats.
Security Posture Evaluation
Assessment extends beyond technical systems to evaluate policies, procedures, and personnel readiness. This includes reviewing access controls, authentication mechanisms, encryption implementations, and security awareness training effectiveness. Documentation review ensures your organization maintains compliance with relevant regulations and industry standards applicable to your sector.
The assessment phase should align with NIST Cybersecurity Framework principles, which provide standardized approaches for managing cybersecurity risk. Many organizations also consult the SANS Institute for advanced security research and training that enhances assessment capabilities.

Containment Strategies for Threat Mitigation
Once threats are identified through assessment activities, containment becomes critical. Effective containment prevents lateral movement, limits data exposure, and enables your team to isolate compromised systems without disrupting business operations. This phase determines whether a minor incident remains contained or escalates into an organization-wide breach.
Network Segmentation and Isolation
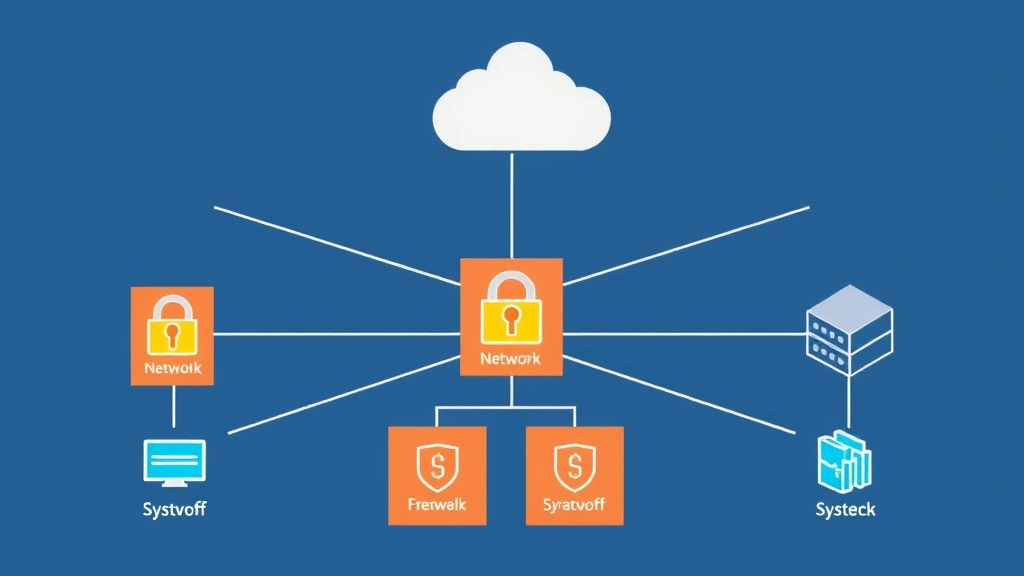
Network segmentation divides your infrastructure into isolated zones, limiting how far an attacker can spread if they penetrate initial defenses. By implementing zero-trust architecture principles, you ensure that every system and user must authenticate and authorize access, regardless of network location. This dramatically reduces the attack surface and containment time when breaches occur.
Access Control Implementation
Least privilege access ensures users and systems have only the minimum permissions necessary for their functions. This principle limits damage if credentials are compromised, as attackers cannot automatically access all organizational resources. Multi-factor authentication adds additional layers, requiring attackers to overcome multiple verification methods rather than relying solely on compromised passwords.
Incident Response Procedures
Containment effectiveness depends on having well-documented incident response procedures that your team has practiced repeatedly. These procedures should define clear escalation paths, communication protocols, and decision-making authorities. Regular tabletop exercises and simulations ensure your team responds effectively when actual incidents occur, minimizing response time and preventing panic-driven errors.
Backup and Recovery Systems
Robust backup systems enable rapid recovery from ransomware and data destruction attacks. Backups should be stored offline or in immutable storage, preventing attackers from encrypting or deleting them. Regular recovery testing ensures your backups function properly and can restore critical systems within acceptable timeframes, reducing business impact from containment activities.
Threat Intelligence and Response Protocols
Threat intelligence transforms raw security data into actionable insights that guide defensive decisions. By understanding current threat actors, their techniques, and their targets, your organization can prioritize defenses and allocate resources effectively. Threat intelligence programs connect assessment findings to real-world attack patterns, revealing which vulnerabilities present the greatest risk to your specific organization.
Intelligence Gathering and Analysis
Threat intelligence comes from multiple sources: internal security logs, industry threat reports, government advisories, and commercial intelligence services. Effective programs correlate data from these sources to identify patterns, attribute attacks to specific threat actors, and forecast emerging threats. This analysis transforms scattered data points into coherent threat pictures that inform strategic security decisions.
Threat Actor Profiling
Understanding who targets your organization—whether nation-states, cybercriminals, or hacktivists—shapes your defensive strategy. Different threat actors employ different techniques, target different assets, and operate with different constraints. Nation-state actors may pursue long-term persistence for espionage, while cybercriminals focus on rapid monetization. Profiling helps your team anticipate attack methods and prioritize defenses accordingly.
Tactical Response Protocols
Threat intelligence enables tactical response protocols that specify how your team should react to specific threat indicators. When your monitoring systems detect indicators of compromise associated with known threat actors, automated or semi-automated responses can immediately isolate affected systems, block malicious IPs, or revoke compromised credentials. This speed of response dramatically reduces attacker dwell time and damage.
Strategic Defense Planning
Long-term threat intelligence programs inform strategic planning, helping organizations invest in defenses that address their greatest risks. If analysis reveals your sector faces sophisticated supply chain attacks, you might prioritize vendor security assessments and software supply chain protections. If data exfiltration represents the primary threat, you might emphasize data loss prevention tools and network monitoring.
Access our comprehensive security insights and expert analysis for additional perspectives on emerging threats and defense strategies. Organizations should also review FireEye’s threat intelligence reports, which provide detailed analysis of advanced persistent threats and emerging attack techniques.
Implementation Best Practices
Successfully implementing ACT Security requires careful planning, stakeholder alignment, and phased deployment. Organizations attempting to implement all components simultaneously often face resource constraints and change management challenges. A structured approach ensures sustainable security improvements without disrupting operations.
Executive Sponsorship and Governance
Effective ACT Security implementation requires executive-level support and clear governance structures. Security leadership must have direct access to executive decision-makers and budget authority to implement necessary changes. Board-level security committees ensure cybersecurity receives appropriate strategic attention and resource allocation alongside other business priorities.
Phased Implementation Approach
Rather than attempting comprehensive implementation immediately, successful organizations phase their efforts. Initial phases focus on assessment activities that establish baseline security posture and identify critical gaps. Subsequent phases address high-risk vulnerabilities and implement containment capabilities. Later phases develop mature threat intelligence programs and optimize response procedures through continuous improvement.
Technology Investment and Tool Selection
While technology cannot solve all security challenges, appropriate tools significantly enhance ACT Security capabilities. Security information and event management (SIEM) systems correlate logs from multiple sources, enabling threat detection. Endpoint detection and response (EDR) tools monitor individual computers for suspicious behavior. Network detection and response (NDR) systems monitor network traffic for indicators of compromise. Tool selection should align with your organization’s specific risks and technical capabilities.
Training and Capability Building
Your security team requires continuous training to maintain current knowledge as threats evolve. Certifications such as CISSP, CISM, and CEH validate expertise and demonstrate commitment to professional development. Beyond formal certifications, hands-on labs, capture-the-flag competitions, and incident response exercises develop practical skills. Security awareness training for all employees ensures non-technical staff understand their role in organizational security.
Vendor and Partner Collaboration
Most organizations cannot address all security challenges independently. Managed security service providers (MSSPs), incident response firms, and security consultants extend internal capabilities. When selecting vendors, verify their expertise aligns with your specific needs and that contractual terms ensure adequate support during security incidents. Regular communication and performance reviews ensure vendor relationships remain productive.
Measuring Security Success
Effective security programs require metrics that demonstrate progress and guide continuous improvement. Unlike many business functions with clear revenue or cost metrics, security success measurement requires carefully designed key performance indicators that reflect actual risk reduction.
Vulnerability Metrics
Track the number of identified vulnerabilities by severity level and average time to remediation. Organizations should establish targets for remediation timelines—critical vulnerabilities within 24-48 hours, high-severity within 1-2 weeks. Declining vulnerability counts and decreasing remediation times demonstrate improving security posture and efficient processes.
Incident Response Metrics
Measure mean time to detect (MTTD) and mean time to respond (MTTR) for security incidents. Declining metrics demonstrate improving detection and response capabilities. Track the percentage of incidents contained within specific timeframes and the percentage requiring escalation, which indicates whether your team can handle incidents appropriately at various levels.
Threat Intelligence Metrics
Evaluate threat intelligence program effectiveness by measuring the percentage of detected incidents attributable to intelligence-guided defenses, the accuracy of threat predictions, and the value of intelligence in preventing incidents. These metrics demonstrate whether intelligence investments translate into actual risk reduction.
Financial and Business Impact Metrics
Ultimately, security investments should reduce organizational risk. Track the number of prevented incidents, estimated cost of prevented breaches, and business continuity improvements. While preventing incidents makes direct financial measurement challenging, estimates based on industry breach costs and your organization’s specific assets provide meaningful perspectives on security ROI.
Compliance and Audit Metrics
Monitor compliance with security policies, regulatory requirements, and industry standards. Track audit findings and remediation status. Declining audit findings and improved compliance demonstrate that security programs are maturing and that policies are actually being followed rather than merely documented.
FAQ
What is the primary difference between ACT Security and traditional security approaches?
ACT Security emphasizes continuous assessment, rapid containment, and threat-informed responses, enabling proactive threat mitigation. Traditional approaches often react only after breaches occur. ACT Security’s structured framework ensures consistent, repeatable processes that improve over time, whereas reactive approaches depend heavily on incident severity and individual responder expertise.
How long does ACT Security implementation typically require?
Implementation timelines vary based on organizational size, current maturity, and resource availability. Assessment phases typically require 2-4 months. Containment capability development requires 3-6 months. Mature threat intelligence programs develop over 6-12 months. Most organizations see meaningful security improvements within 6 months and substantial improvements within 12-18 months of committed implementation.
Can small organizations implement ACT Security effectively?
Absolutely. While large enterprises may have dedicated security teams, small organizations can implement ACT Security through prioritization and vendor partnerships. Focusing initial efforts on assessment and critical vulnerability remediation, then gradually building containment and threat intelligence capabilities, allows sustainable progress regardless of organization size. Managed security service providers can supplement internal capabilities.
How does ACT Security relate to compliance requirements like HIPAA or PCI-DSS?
ACT Security frameworks align with and often exceed compliance requirements. While regulations specify minimum security standards, ACT Security provides comprehensive approaches that address both regulatory requirements and emerging threats. Organizations implementing ACT Security typically achieve compliance more effectively because the frameworks embed compliance controls within broader security strategies rather than treating compliance as separate from security.
What metrics best demonstrate ACT Security program success?
The most meaningful metrics include declining vulnerability remediation times, decreasing mean time to detect and respond for incidents, reduced incident severity and frequency, improved compliance audit results, and estimated prevention of breaches based on industry data. Executive dashboards should emphasize business impact metrics alongside technical metrics, demonstrating that security investments reduce organizational risk.
How should organizations prioritize between assessment, containment, and threat intelligence investments?
Initial investments should emphasize assessment because you cannot protect what you don’t know about. Once assessment reveals critical vulnerabilities and risks, containment capabilities address the highest-risk items. Threat intelligence investments mature as your organization gains experience with incidents and develops understanding of relevant threat actors. This phased approach ensures each investment builds on previous work and delivers measurable value.


